Last Updated: 2024-10-14
Purpose
This article serves to improve understanding of the role that assessment scans play in enhancing the security and resilience of an organization's digital infrastructure. It provides an overview of the objectives and configurations of various assessments, including Application Assessment, Docker Image Assessment, Cloud Assessment, Network Host Assessment, and Agent Assessment.
Technical Preview
This article contains parts that are technical previews of features that is currently under development. These features may be hidden behind a feature flag.
Introduction
The Scan Assessment Configuration feature in Outpost24 lets you define how security assessments are applied across different asset types—whether it is web applications, Docker images, cloud infrastructure, network hosts, or agents. It shapes which assets are targeted, how deep the scanning should go, and which policies apply, so your vulnerability management efforts are precise and relevant to each environment. In doing so, it ensures that each scan aligns with its intended context and helps surface meaningful findings for remediation.
Scan Assessment
Vulnerability and Compliance assessments target a set of assets and identify findings that is presented and tied to the scanned assets.
Application Assessment
-
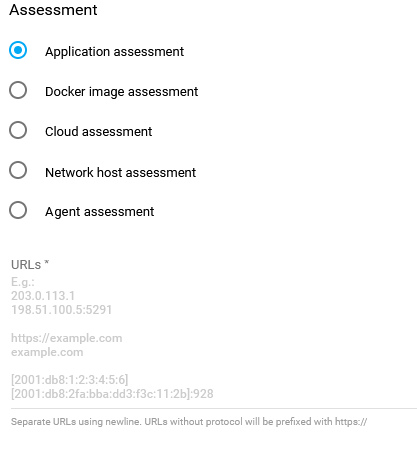
Select Application assessment.
-
Fill in the targets.
When adding more than one target, separate them using a new line.
The targets can be added as:-
URL -
https://example.com -
IPv4 -
203.0.113.1 -
IPv4:port -
198.51.100.5:5291 -
IPv6 -
[2001:db8:1:2:3:4:5:6] -
IPv6:port -
[2001:db8:2fa:bba:dd3:f3c:11:2b]:928 -
Hostname -
cumulus
-
-
After adding the targets, click the blue ADD button in the lower right corner.
URL-entries not starting with https protocol are prefixed with https://.
A configuration name is extracted from the host, optional port and path to build a unique and user-friendly representation of the added configuration. URL fragments and queries are not used for configuration names.
Example inputs and generated configuration names:
-
https://example.com/ > example.com
-
https://example.com:8080/admin/login/ > example.com:8080/admin/login
-
https://example.com:8080/admin/#/login > example.com:8080/admin
-
https://example.com:8080/admin?relogin=true > example.com:8080/admin
-
http://192.0.2.99:8081 > 192.0.2.99:8081
The Choose scanner (HIAB only) option is visible if at least one Appsec scanner is available.
-
The first scanner in the list is selected by default.
-
The selected scanner can be changed in the Edit view.
To add scans in HIAB Appsec, one of the regular HIAB scanners must be turned into Appsec scanner.
See Setting up a HIAB as an Appsec Scale Scanner for more information.
Setting up the Application Assessment
-
Select Application assessment.
-
Fill in the targets.
When adding more than one target, separate them using a new line.
The targets can be added as:-
URL -
https://example.com -
IPv4 -
203.0.113.1 -
IPv4:port -
198.51.100.5:5291 -
IPv6 -
[2001:db8:1:2:3:4:5:6] -
IPv6:port -
[2001:db8:2fa:bba:dd3:f3c:11:2b]:928 -
Hostname -
cumulus
-
-
After adding the targets, click the blue ADD button in the lower right corner.
URL-entries not starting with https protocol are prefixed with https://.
A configuration name is extracted from the host, optional port and path to build a unique and user-friendly representation of the added configuration. URL fragments and queries are not used for configuration names.
Example inputs and generated configuration names:
-
https://example.com/ > example.com
-
https://example.com:8080/admin/login/ > example.com:8080/admin/login
-
https://example.com:8080/admin/#/login > example.com:8080/admin
-
https://example.com:8080/admin?relogin=true > example.com:8080/admin
-
http://192.0.2.99:8081 > 192.0.2.99:8081
The Choose scanner (HIAB only) option is visible if at least one Appsec scanner is available.
-
The first scanner in the list is selected by default.
-
The selected scanner can be changed in the Edit view.
To add scans in HIAB Appsec, one of the regular HIAB scanners must be turned into Appsec scanner.
See Setting up a HIAB as an Appsec Scale Scanner for more information.
Docker Image Assessment
The Docker image assessment evaluates the security risks and vulnerabilities associated with the Docker images used by an organization. Docker images are pre-configured software packages that contain all the necessary components to run an application and can be easily distributed and deployed in a container environment.
A Docker Image Assessment involves tools to identify the contents of the image and assess the security of the software components, including the operating system and any applications or services included in the image. Configuration errors or misconfiguration can create security vulnerabilities that can be exploited by attackers.
The results of Docker Image Assessments are used to prioritize vulnerabilities and develop a remediation plan. It may include updating the image with the latest security patches or configurations.
It is essential that Docker Image Assessments should be conducted regularly, as new vulnerabilities can be introduced as software is updated or new images are created.
Requirements
To access a private registry, a Docker account with its credentials are required.
When scanning a Docker image using OUTSCAN RC, a HIAB deployed as a container inspection scanner is required. For more information, see Use Appsec Scale with OUTSCAN RC.
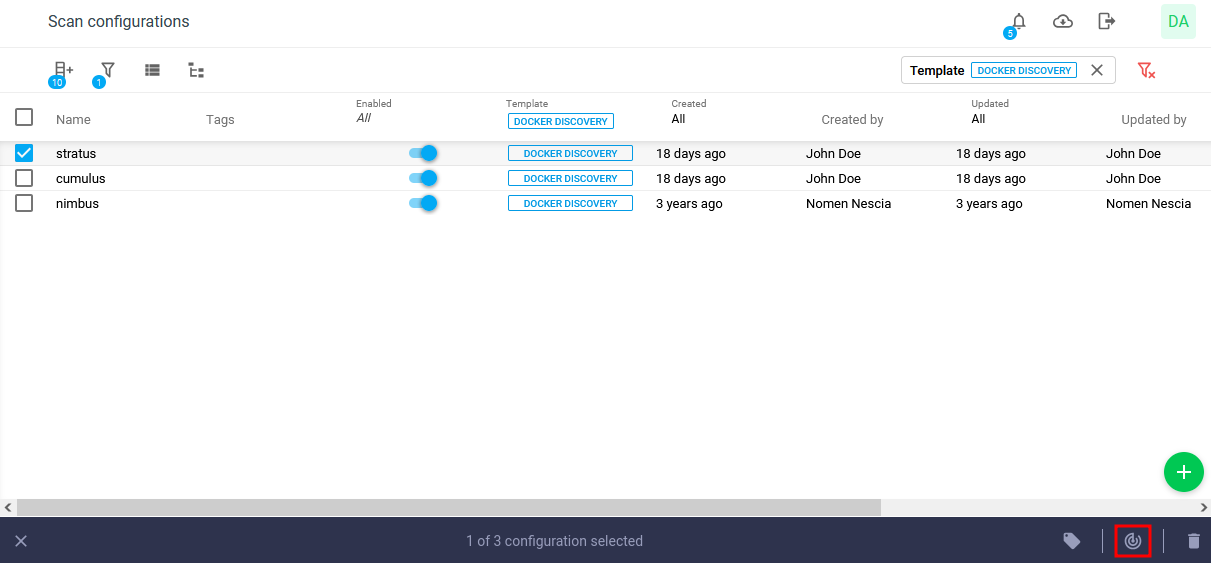
HIAB and OUTSCAN RC supports a Docker image scan. You can scan a Docker image if you have done a Docker discovery to retrieve the images available on your private Docker Registries.
Currently, it is only possible to scan images that are less than 1GB and type of Linux and with a 64 bit architecture.
Setting up the Docker Image Assessment
Follow the below procedure to scan Docker images:
-
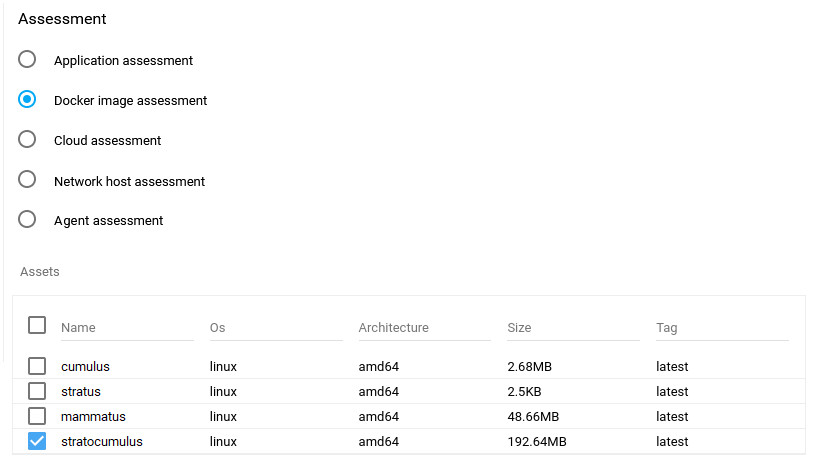
To create a Docker image assessment scan configuration, select Docker image assessment under Assessment.
-
Select Assets from the table displaying all the discovered images and the details of an image such as name, OS, architecture and size.
-
The Max Concurrent Scans field sets the maximum number of scans that can run at the same time. Set the value to 0 for no limit.
-
The Max Concurrent scans per asset field determines how many scans can concurrently run against a single asset. Set the value to 0 disables this restriction.
-
Select one or more images and click on ADD to save the scan configuration. The name of the scan configuration can be changed by editing it.
-
Click on the scan now

-
View the scan status under Scans. Click on Scans on the Toolbar to view all scans performed on HIAB with the status starting 'QUEUED, STARTING, RUNNING, FINISHED'.
-
To view the vulnerability set of the scanned image, click on Findings in the menu, and select Vulnerabilities.
By default all Docker image vulnerabilities are displayed. You can filter the result by selecting All, No or Yes in the Potential column respectively.
-
All: view all vulnerabilities.
-
No: excluding any potential vulnerabilities.
-
Yes: view only potential vulnerabilities without a fix.
To display the Potential item in the column, select it from the column list ![]()
The potential vulnerabilities are marked in the potential column with a green dot.
You can then select within the potential column the option you want.
See Scan a Docker Image for more information.
Cloud Assessment
Cloud environments can introduce new risks and vulnerabilities that may not exist in traditional on-premises environments. This makes cloud assessments an important part of any Vulnerability Management program. The Cloud Assessment evaluates compliance against a policy in a Boolean way regarding an organization's use of cloud services.
A Cloud Assessment evaluates the customer's use of the cloud service provider, as well as assessing the configuration and security of the organization's own cloud environment. This can include evaluating the security of the network architecture, access controls, and data encryption.
The assessment considers the unique security challenges to be associated with different types of public cloud deployments, such as AWS, Google Cloud, and Azure. For example, a public cloud environment may require additional controls to protect against data breaches and unauthorized access, while a private cloud environment may require more focus on access controls and network segmentation.
The assessment identifies potential vulnerabilities and risks and is used to develop plans for remediation. This includes implementing additional security controls or practices, such as multi-factor authentication, network segmentation, or regular vulnerability scanning and testing.
In summary, a cloud assessment is a critical component of maintaining a secure cloud environment and should be conducted on a regular basis to ensure ongoing protection against emerging threats and vulnerabilities.
Setting up the Cloud Assessment
-
Select which assessment to use, for this example Cloud assessment is chosen.
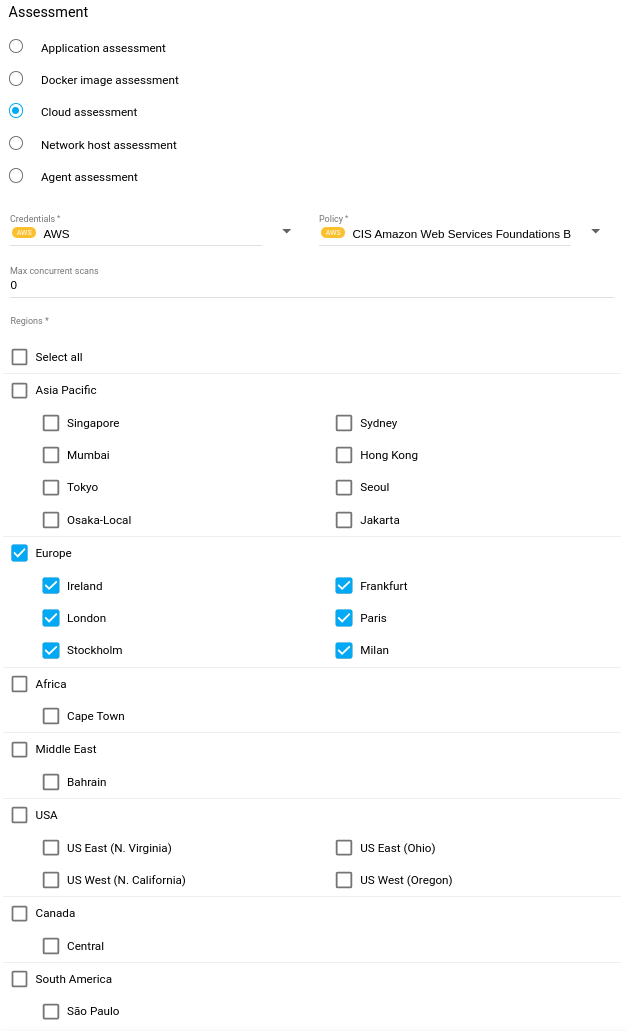
-
Select Credentials from the drop down menu. See Scan Credentials for more information on how to set up scan credentials.
Whenaws.access.key.allow.remote = falseand ARN credentials are selected, the scanner dropdown is hidden and the default scanner is selected as value. -
Select Policy from the drop down menu.
-
The Max Concurrent Scans field sets the maximum number of scans that can run at the same time. Set the value to 0 for no limit.
-
Select which Regions to scan. For further information about AWS regions, see https://docs.aws.amazon.com/AWSEC2/latest/UserGuide/using-regions-availability-zones.html.
If multiple regions are selected, each time the scan configuration runs, the number of scans queued/started will match the number of regions selected. -
Click on the blue Add button in the lower right corner to add the configuration.
Adding new configurations also populates the Assets. The assets are deducted from the submitted target information. If an asset already exists, the created configuration is linked to it. Else, it is created upon creation of the configuration and linked.
See Cloudsec Scan Configuration for more information.
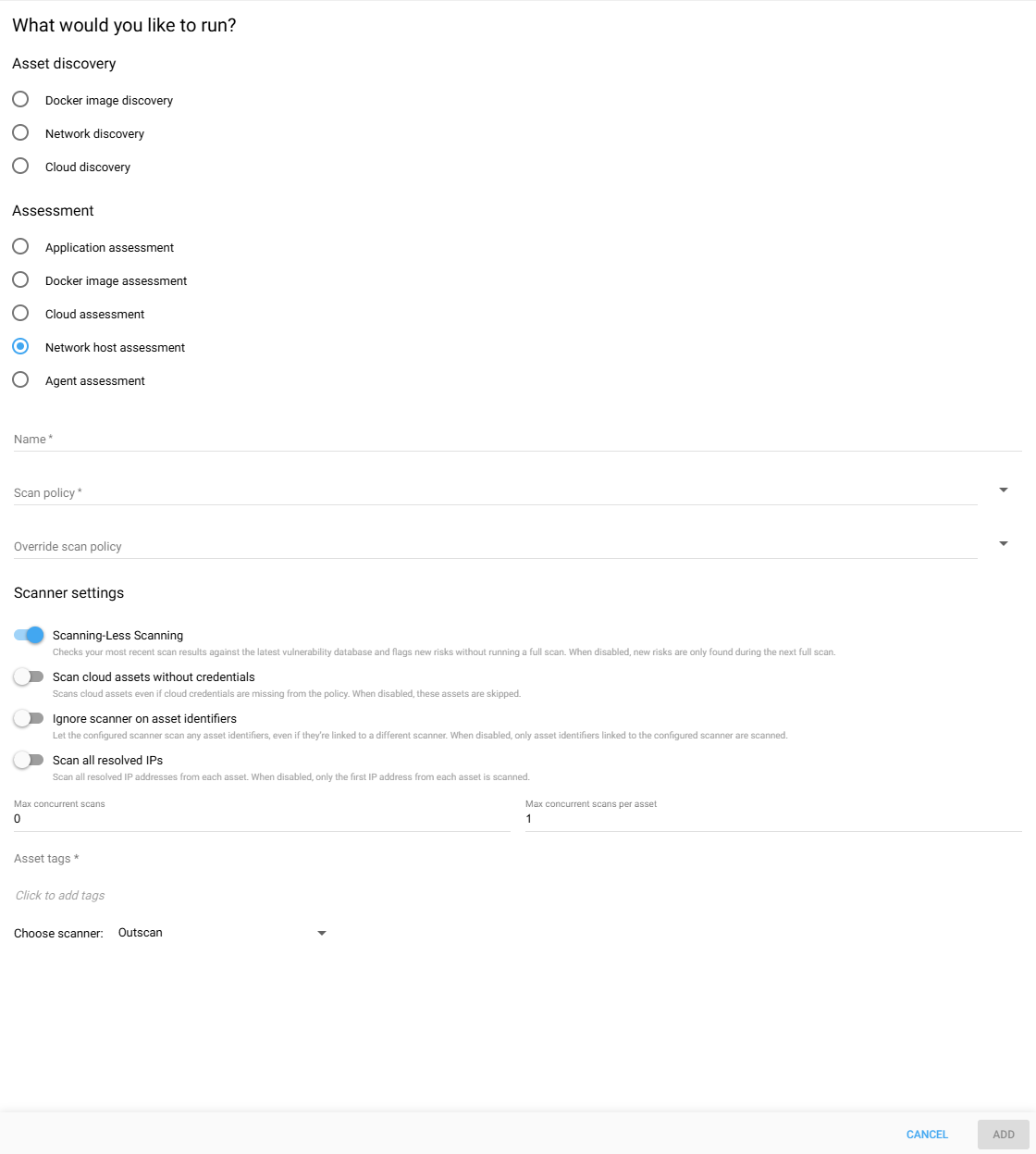
Network Host Assessment
-
Select Network host assessment.
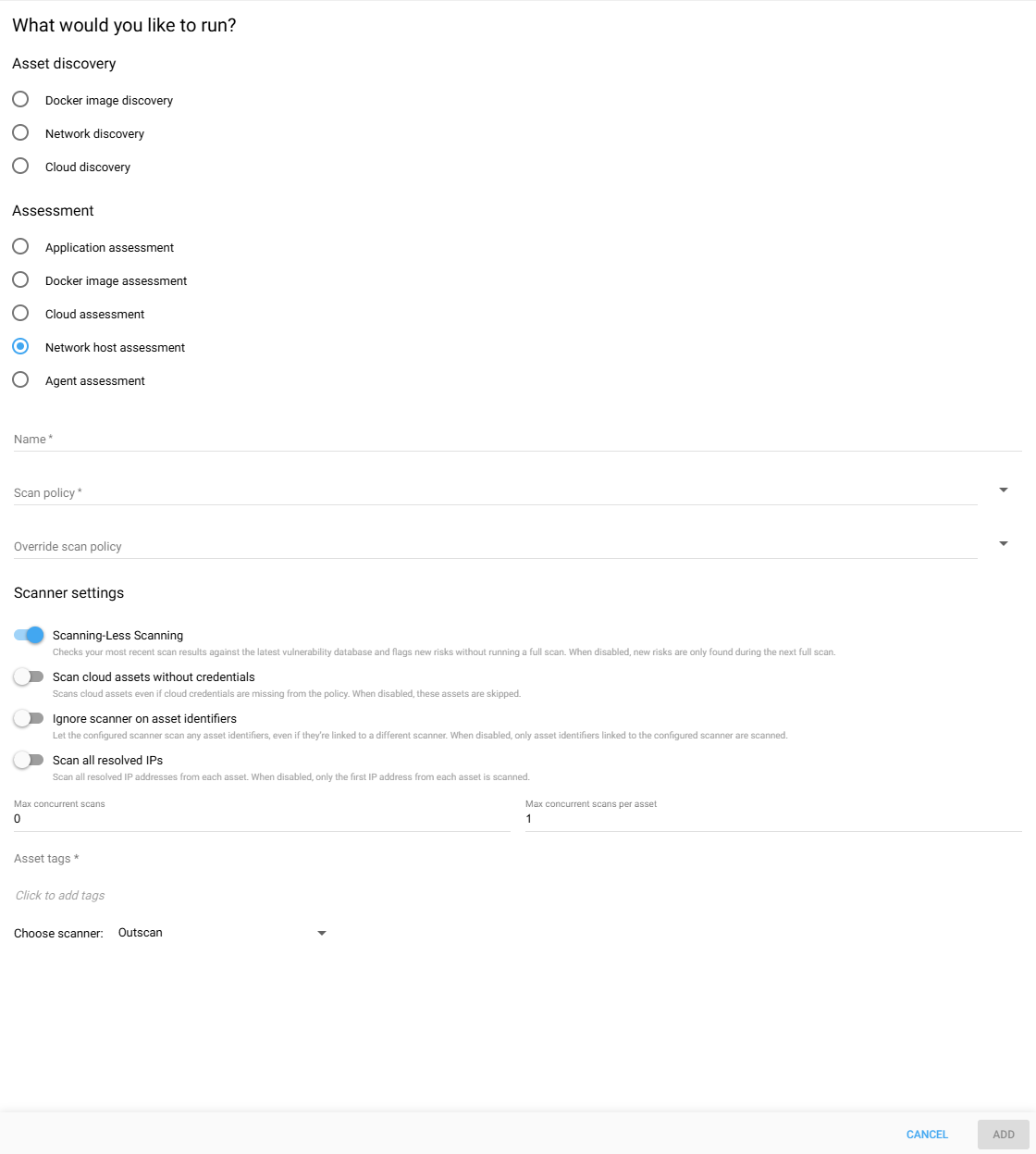
-
Fill in the Name input field with a descriptive name for the intended assessment.
-
Select Policy from the drop-down menu. To create a new scan policy, refer to: Scan Policies.
-
Optionally, select an Override scan policy from the drop-down menu. For a more detailed description of this parameter, refer to: Policy Settings.
-
Toggle the Scanning-Less Scanning switch button to enable or disable this option. For a comprehensive understanding of this feature, refer to: Scanning-Less Scanning.
-
Toggle the Scan Cloud Assets Without Credential switch to continue scanning assets even if no cloud credentials are found. If disabled, such assets will be skipped.
-
If the Ignore scanner on asset identifiers switch is disabled, asset associations will only be scanned using scanners that match the specified scanner field. Otherwise, they can be scanned with any available scanner.
-
If the Scan all resolved IPs switch button is enabled, the scan will scan all the IP addresses resolved from assets. Otherwise, only the first resolved IP address will be scanned.
-
The Max Concurrent Scans field sets the maximum number of scans that can run at the same time. Set the value to 0 for no limit.
-
The Max Concurrent scans per asset field determines how many scans can concurrently run against a single asset. Set the value to 0 disables this restriction.
-
Select Asset tags to filter which assets are included in the scan. You can select multiple tags, and only assets that contain all of the selected tags will be scanned. For example, if you select
worldwideandlocation:hanoi, only assets that have both tags will be included (This is especially useful when you want to narrow down scans for more precise targeting). -
Click on the blue Add button in the lower right corner to add the configuration.
Setting up a Network Assessment
-
Select Network host assessment.
-
Fill in the Name input field with a descriptive name for the intended assessment.
-
Select Policy from the drop-down menu. To create a new scan policy, refer to: Scan Policies.
-
Optionally, select an Override scan policy from the drop-down menu. For a more detailed description of this parameter, refer to: Policy Settings.
-
Toggle the Scanning-Less Scanning switch button to enable or disable this option. For a comprehensive understanding of this feature, refer to: Scanning-Less Scanning.
-
Toggle the Scan Cloud Assets Without Credential switch to continue scanning assets even if no cloud credentials are found. If disabled, such assets will be skipped.
-
If the Ignore scanner on asset identifiers switch is disabled, asset associations will only be scanned using scanners that match the specified scanner field. Otherwise, they can be scanned with any available scanner.
-
If the Scan all resolved IPs switch button is enabled, the scan will scan all the IP addresses resolved from assets. Otherwise, only the first resolved IP address will be scanned.
-
The Max Concurrent Scans field sets the maximum number of scans that can run at the same time. Set the value to 0 for no limit.
-
The Max Concurrent scans per asset field determines how many scans can concurrently run against a single asset. Set the value to 0 disables this restriction.
-
Select Asset tags to filter which assets are included in the scan. You can select multiple tags, and only assets that contain all of the selected tags will be scanned. For example, if you select
worldwideandlocation:hanoi, only assets that have both tags will be included (This is especially useful when you want to narrow down scans for more precise targeting). -
Click on the blue Add button in the lower right corner to add the configuration.
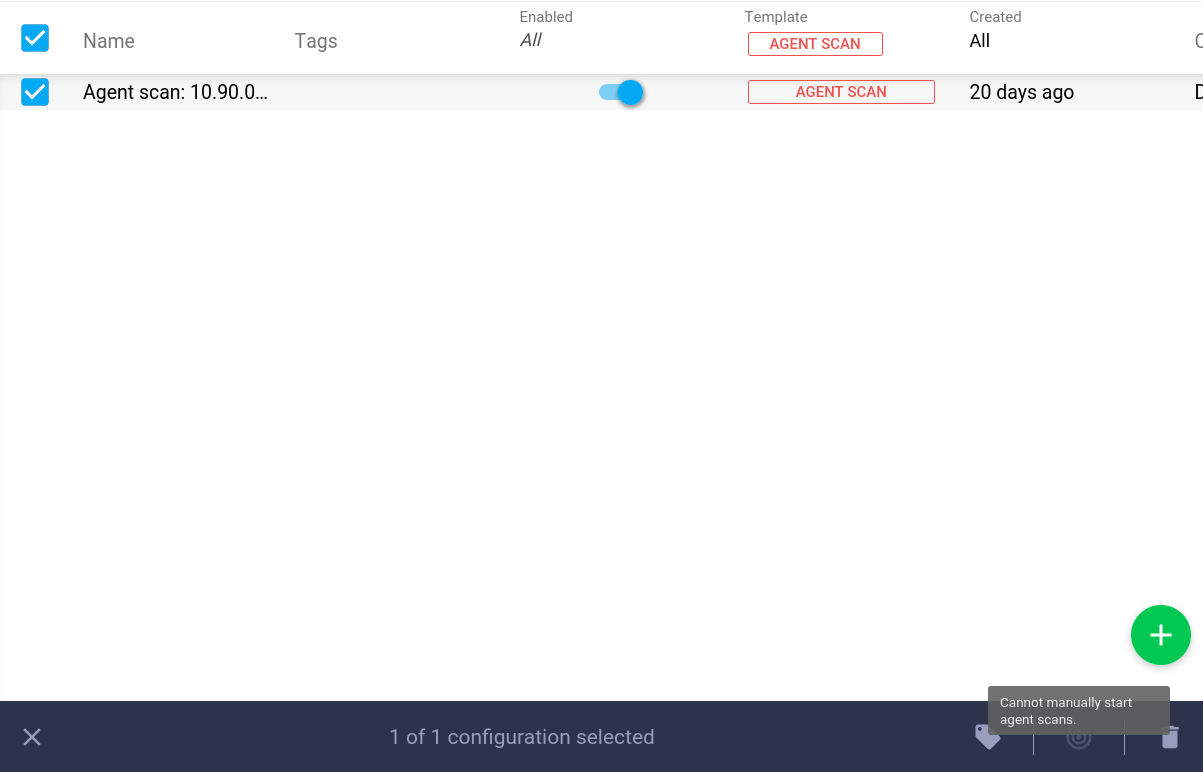
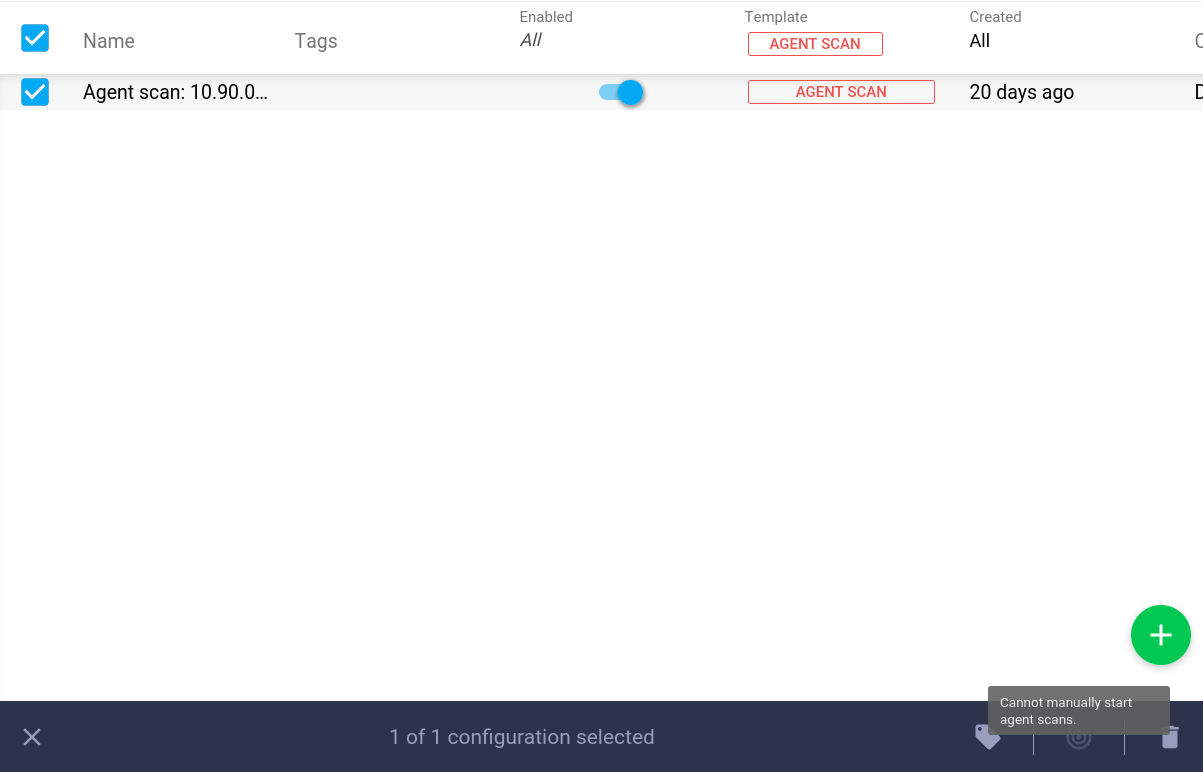
Agent Assessment
-
Select Agent assessment.
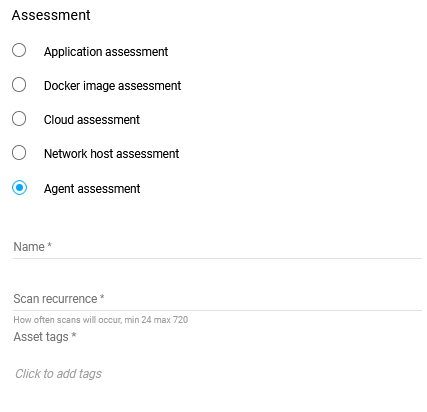
-
Fill in the Name input field with a descriptive name for the intended assessment.
-
Enter a value in the Scan Recurrence field to specify the scan recurrence in hours. The minimum frequency is 24 hours, and the maximum is 30 days.
-
Asset Tags
-
Click on the blue Add button in the lower right corner to add the configuration.
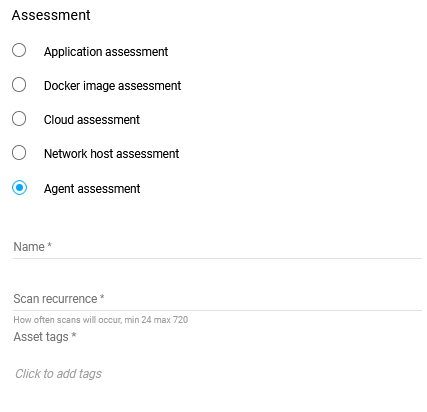
Running Agent assessment manually from the Scan configuration is not supported, so the Scan Now button is disabled and cannot start agent scans.
Agents are asynchronous in their behavior, and are not connected to Outscan to "receive" scans when started like HIABs. Instead the agent has a duration between each scan in hours with an allowed range of 24-720 (1d-30d). When the data from an agent has been fully received, Outscan then runs reporting to complete the scan.
Setting up a Agent Assessment
-
Select Agent assessment.
-
Fill in the Name input field with a descriptive name for the intended assessment.
-
Enter a value in the Scan Recurrence field to specify the scan recurrence in hours. The minimum frequency is 24 hours, and the maximum is 30 days.
-
Asset Tags
-
Click on the blue Add button in the lower right corner to add the configuration.
Running Agent assessment manually from the Scan configuration is not supported, so the Scan Now button is disabled and cannot start agent scans.
Agents are asynchronous in their behavior, and are not connected to Outscan to "receive" scans when started like HIABs. Instead the agent has a duration between each scan in hours with an allowed range of 24-720 (1d-30d). When the data from an agent has been fully received, Outscan then runs reporting to complete the scan.
References
Related Articles
- Windows 10/Windows 2019 Server
- General Information about SMB/WinRM Scanning
- Windows 8.1
- Scan Blueprint
- How to Test SMB Authentication
- Docker Image Assessment
- Windows 2016 Server
- How to Scan AWS ECR Images
- Scanning-Less Scanning
- Scan Scheduling Errors
- Network Host Assessment
- Core Installation
- Windows 2008 R2 Server
- Scanning Range
- SMB Authentication from OUTSCAN/HIAB
