Last Updated: 2025-05-27
Purpose
This article provides users with a overview of scanning a Docker image using HIAB and Outscan RC.
Introduction
In Outpost24, the Cloud Assessment feature lets you evaluate your cloud infrastructure’s security posture against defined policies. It inspects not only how you use cloud services like AWS, Azure, or GCP, but also your configuration choices—such as network layout, access controls, encryption, and permissions. Because cloud environments have unique risks compared to on-premises systems, running these assessments helps you identify misconfigurations, compliance gaps, and vulnerabilities specific to your cloud setup, enabling more effective remediation and ongoing risk management.
Requirements
A Docker account with its credentials to access a private registry.
When scanning a Docker image using OUTSCAN RC, a HIAB deployed as a container inspection scanner is still required.
For more information see Use Appsec Scale with OUTSCAN RC
Steps to Scan a Docker Image
A Docker image is a file used to execute code in a Docker container. Docker images act as a set of instructions to build a Docker container, like a template. Docker images also act as the starting point when using Docker. An image is comparable to a snapshot in virtual machine (VM) environments.
To scan a Docker image
-
Add your private Docker registries to HIAB.
-
Run a Docker image discovery to retrieve the list of available images.
-
Run a Docker image assessment (Docker scan) on a selected image to get the vulnerability assessment.
Docker scan capability can be enabled/disabled on your HIAB. Contact Outpost24 Support for more information.
Configure Docker Registry Credentials
Configure Docker registry credentials in Outpost24: enter registry URL, username/password, upload PEM certificate if self-signed for secure image pulls.
Run a Docker Image Discovery Scan
A Docker Registry discovery function retrieves images information from a private Docker Registry such as name, OS, architecture and size.
-
Prior to running a Docker discovery, make sure you have created the Docker credentials.
-
The discovery will only find Docker image with latest tag to limit number of Docker images and improve visibility.
To perform a Docker discovery,
-
Navigate to Configuration > Scan Configurations in the Main Menu.
-
Click on the
-
Select Docker image discovery, fill the required information and choose the scanner.
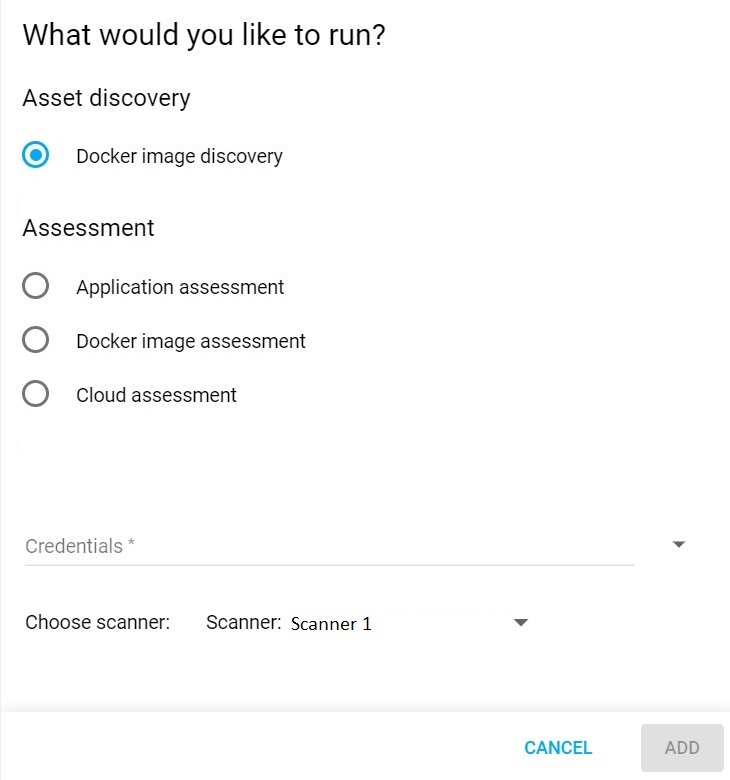
Docker Image Discovery
-
Click on ADD to save the newly created configuration.
-
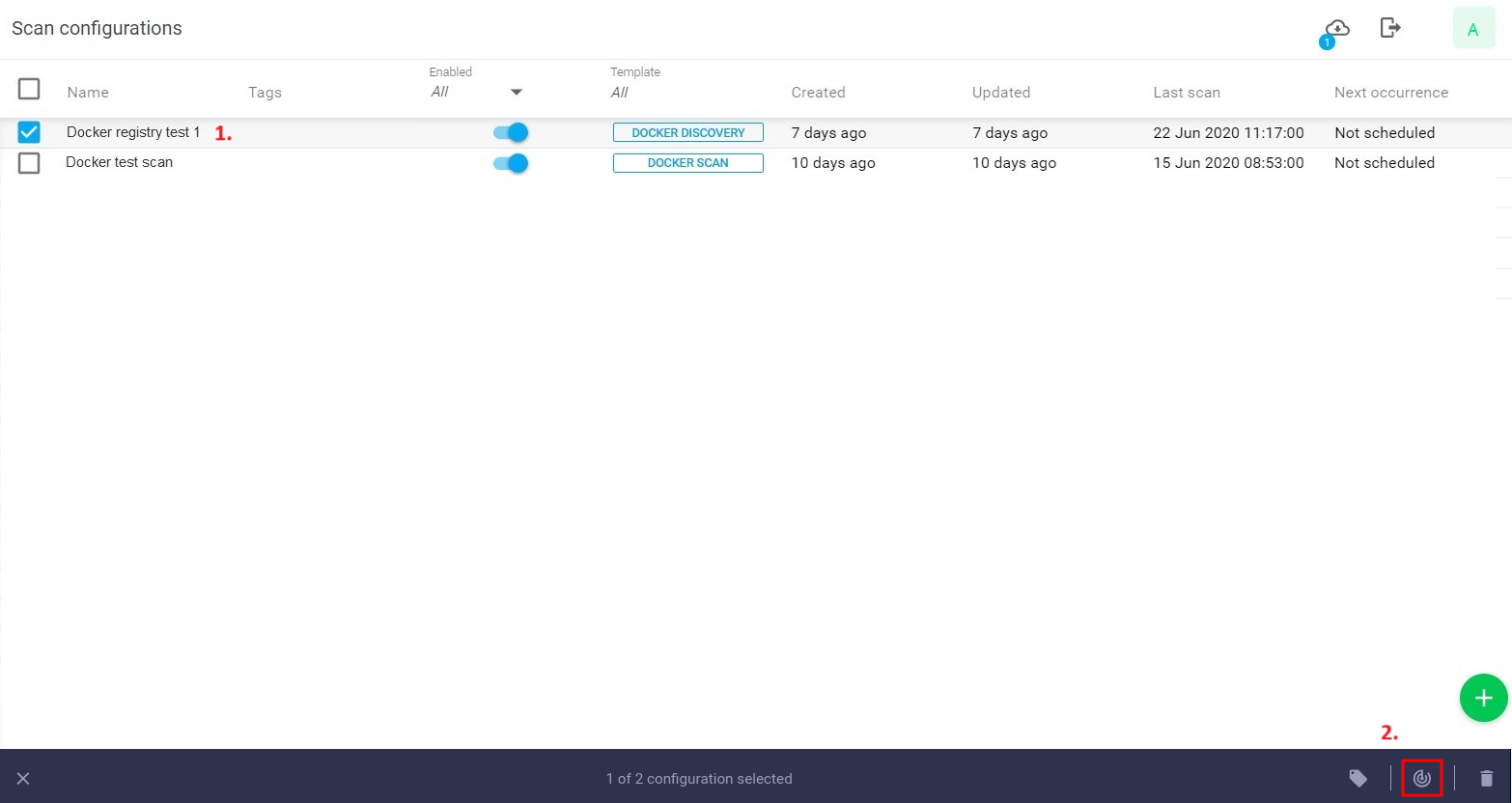
Select the scan configuration and click on the scan now

-
View the scan status under Toolbar/ Scans.
-
View discovered assets, Docker images under Assets as the list of assets with 'source' set to Cloudsec and type set to Docker Image.
.png?cb=d61b67be2676d45d0c1cd11d6a1b81e4)
Run a Docker Image Assessment Scan
HIAB and OUTSCAN RC supports a Docker image scan. You can scan a Docker image if you have done a Docker discovery to retrieve the images available on your private Docker Registries.
Currently, it is only possible to scan image that are less than 1GB and type of Linux and with a 64 bit architecture.
Follow the below procedure to scan Docker images:
-
Create a Docker image assessment scan configuration. Select Docker image assessment under Assessment then select the Docker credential you want to scan.
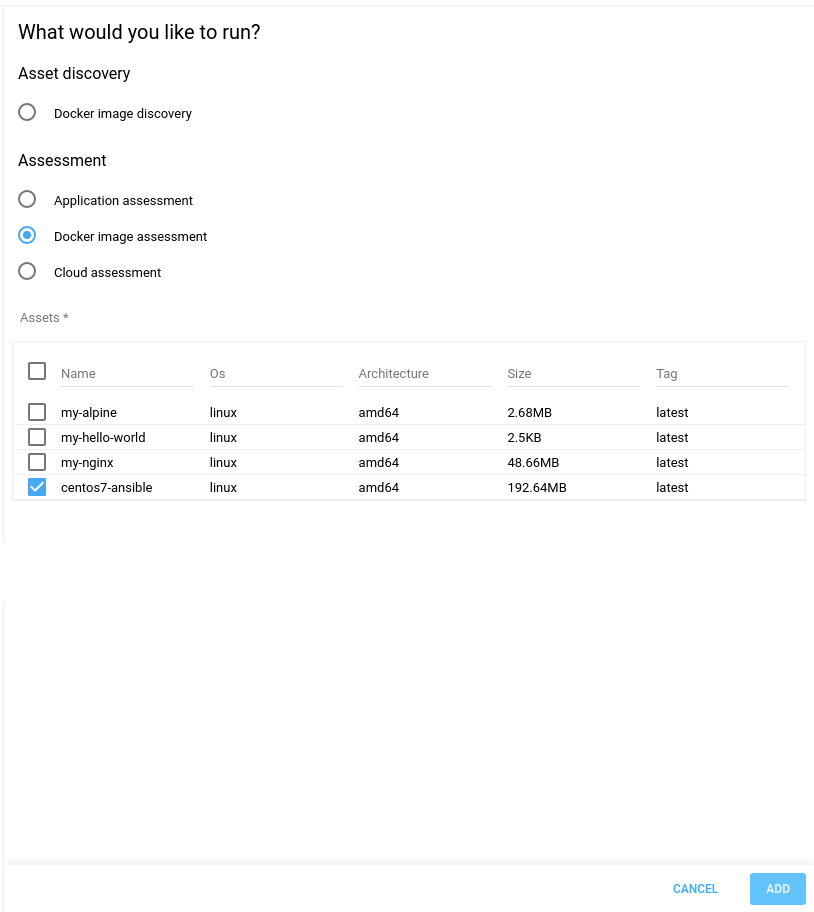
-
On Docker credentials selection, a table is displayed with all the discovered images and the details of an image such as name, OS, architecture and size.
-
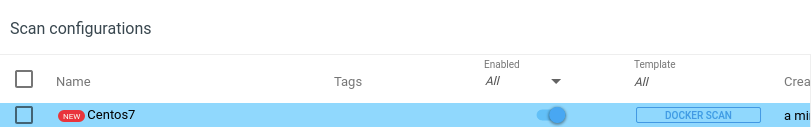
Select one or more images and click on ADD to save the scan configuration. The name of the scan configuration can be changed by editing it.
-
Click on Scan Now to run the Docker image assessment scan.
-
View the scan status under Scans.
Click on Scans on the Toolbar to view all scans performed on HIAB with the status starting 'QUEUED, STARTING, RUNNING, FINISHED'.
-
To view the vulnerability set of the scanned image, click on Findings, and select Vulnerabilities.
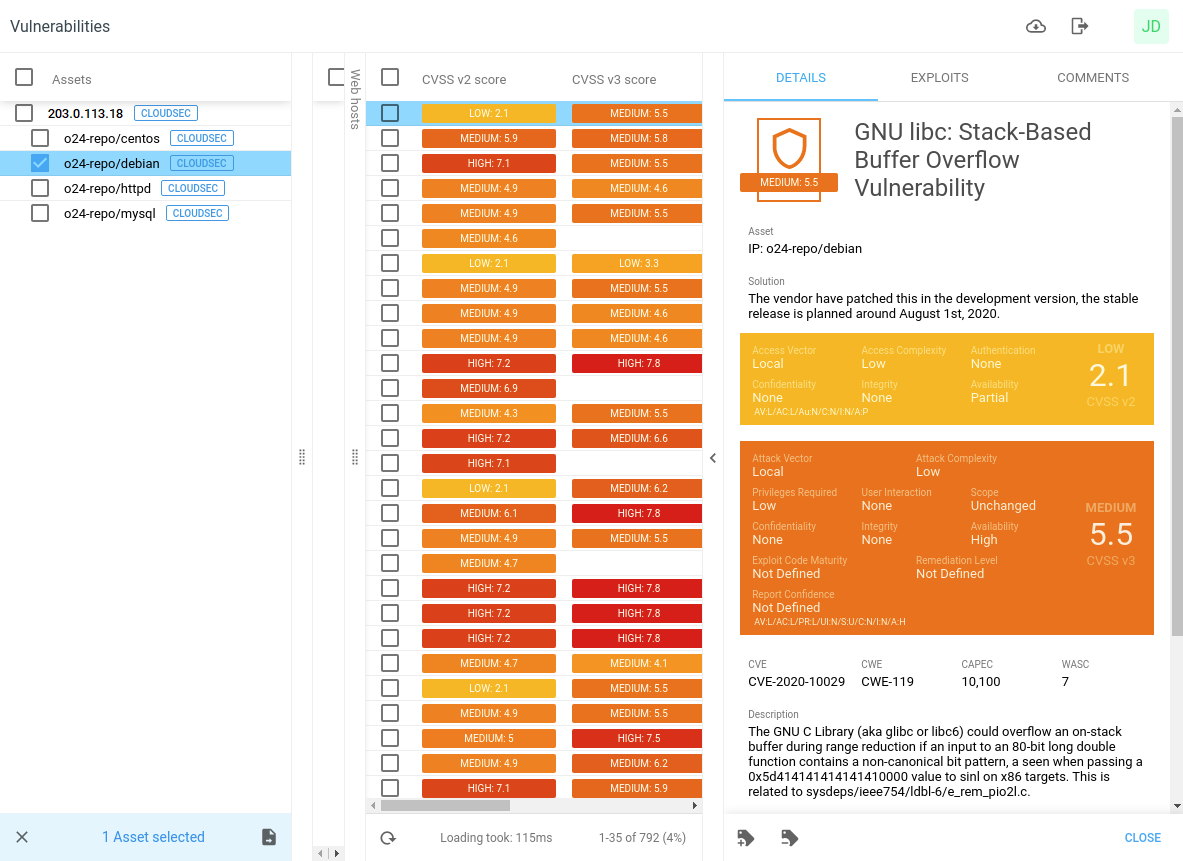
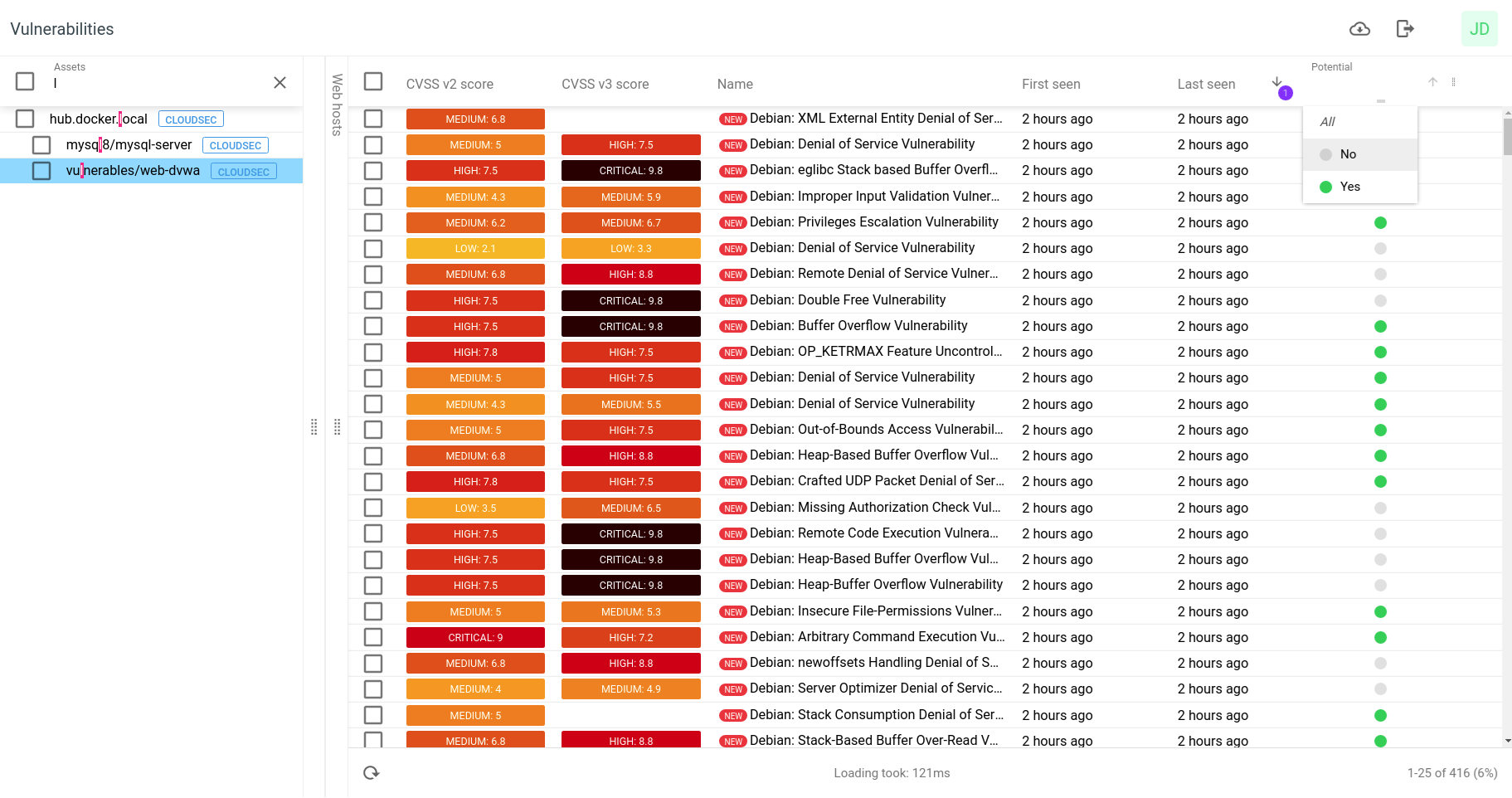
By default all Docker image vulnerabilities are displayed. You can filter the result by selecting All, No or Yes respectively.
-
All: view all vulnerabilities
-
No: excluding any potential vulnerabilities
-
Yes: view only potential vulnerabilities without fix
To display the Potential item in the column, select it from the item list and check the corresponding box.
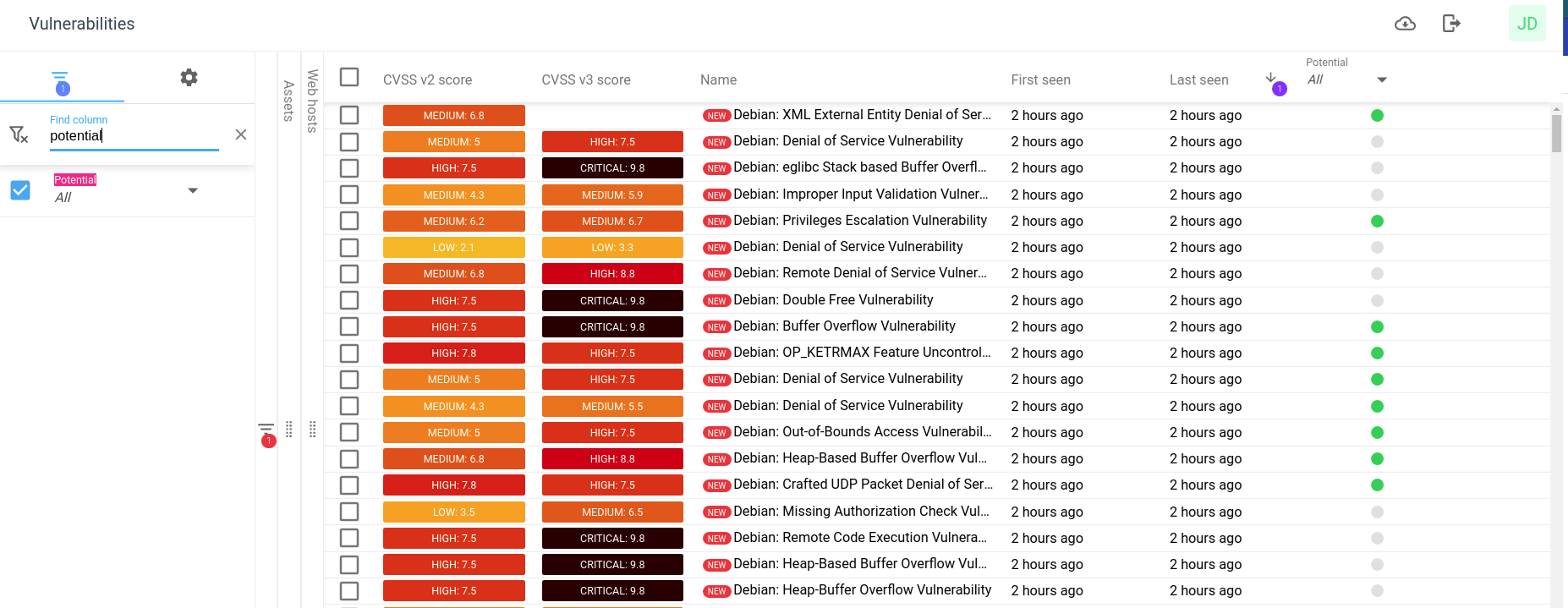
The potential vulnerabilities are marked in the potential column with a green dot.
Then you can select within the potential column the option you want.
Related Articles
- Windows 10/Windows 2019 Server
- General Information about SMB/WinRM Scanning
- Windows 8.1
- Scan Blueprint
- How to Test SMB Authentication
- Docker Image Assessment
- Windows 2016 Server
- How to Scan AWS ECR Images
- Scanning-Less Scanning
- Scan Scheduling Errors
- Network Host Assessment
- Core Installation
- Windows 2008 R2 Server
- Scanning Range
- SMB Authentication from OUTSCAN/HIAB
