Last updated: 2018-09-26
Purpose
This article provides setup information on the ArcSight integration.
Introduction
The ArcSight integration enables the HIAB appliance to forward vulnerability and system events to an ArcSight Security Information and Event Management (SIEM) platform. ArcSight, originally developed by HP, uses a syslog-based mechanism to collect and analyze security events from multiple systems. When this integration is enabled on HIAB, syslog events generated by the platform are formatted specifically for ArcSight and transmitted to an ArcSight logger or connector for processing.
By sending vulnerability scanning events and related data to ArcSight, organizations can include information from their Outpost24 environment in a centralized security monitoring platform. The ArcSight-formatted messages structure event data into defined fields, making it easier for the SIEM to parse, categorize, and analyze the information compared to raw syslog messages. This allows security teams to correlate vulnerability findings with other security telemetry and operational logs within the SIEM. Integrating HIAB with ArcSight therefore improves visibility into scanning activity, supports centralized security monitoring, and helps organizations respond more effectively to detected risks across their infrastructure.
Prerequisities
Before enabling ArcSight in the HIAB, the ArcSight server needs to be set up and configured.
Set Up ArcSight
To enable ArcSight:
-
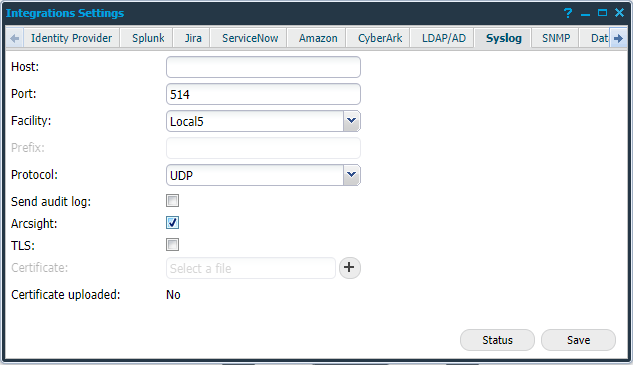
Go to Menu > Settings > Integrations.
-
Select the Syslog tab.
-
Check the Arcsight: checkbox as shown in the figure.
-
Click Save.
When ArcSight is enabled, the Syslog message is built differently to fit into the ArcSight protocol.
Using ArcSight
When a Syslog event is activated, an ArcSight message is built instead of the ordinary Syslog message.
The Syslog message is sent to the ArcSight logger or the connector. When the logger shows the message, it is divided into columns that is easier to work with than the raw data.
No ArcSight specific errors should occur. If the ArcSight server has errors it is due to the Syslog implementation, not the ArcSight implementation.
It is recommended that the customer uses ArcSight together with TLS. If the logger cannot work with the TLS messages, a connector is recommended to be able to do so.
There is no maintenance needed for ArcSight, but the logger or the Syslog settings must be updated if IP numbers or other information are switched.
Examples:
A Syslog Message
Risk: Script Name: "Unencrypted Remote Authentication Available - POP3" Script Id: "219784" Target: "192.168.202.6" Port: "110" BugTraq: "No bugtraq" CVSS: "6.8" New: "0" CVE: "No CVE" Family: "pop3" First Seen: "2016-11-21 11:08" Last Seen: "2016-11-24 18:06" Product: "Unencrypted Remote Authentication" Has Exploits: "false" – Medium
An ArcSight Message
dvc=192.168.202.6 spt=110 cs1Label=Script Name cs1=Unencrypted Remote Authentication Available - POP3 cs4Label=BugTraq cs4=No bugtraq cs2Label=CVE cs2=No CVE deviceCustomDate1Label=First Seen deviceCustomDate1=Nov 21 2016 11:08:00 deviceCustomDate2Label=Last Seen deviceCustomDate2=Nov 24 2016 18:08:00 msg=Script Id: 219784 New: 0 Family: pop3 Product: Unencrypted Remote Authentication Has Exploits: false
Related Articles
- ServiceNow - Legacy
- Identity Provider Settings
- Okta Identity Provider Configuration
- Database Connector (HIAB only)
- Microsoft Entra ID (Azure AD) Identity Provider Configuration
- SNMP (HIAB only)
- ADFS Identity Provider Configuration
- Splunk
- Amazon
- Atlassian Jira
- Syslog (HIAB only)
- Thycotic
- OneLogin Identity Provider Configuration
- CyberArk
- LDAP/AD
