Last updated: 2026-02-18
Purpose
This article provides users with a overview of Asset Groups.
Introduction
Asset Groups in Outpost24 serve as organizational units that group multiple assets—distinct resources identified by IP addresses, hostnames, Docker images, cloud accounts, etc.—for streamlined vulnerability management and reporting. For users engaging with the AppSec Asset Management module, these groups are accessible through the Asset Groups tab, offering visibility into remediation status, vulnerability trends, and CVSSv3 metrics.
Asset Groups provide both high-level visibility and granular insights into the security posture of collections of assets. The dashboard’s visual cards and group-level details facilitate efficient vulnerability tracking and remediation planning. However, it's worth noting that for deeper operations—such as dynamic inclusion based on tags, inheritance, and automation—Outpost24 also offers Dynamic Asset Groups, which operate using tag-based logic for automatic population and maintenance
Prerequisites
The reader needs basic access to the OUTSCAN™ account with an active SWAT subscription to interact with groups in Managed section.
For more information about the Portal see Getting Started with the Portal.
Dashboard
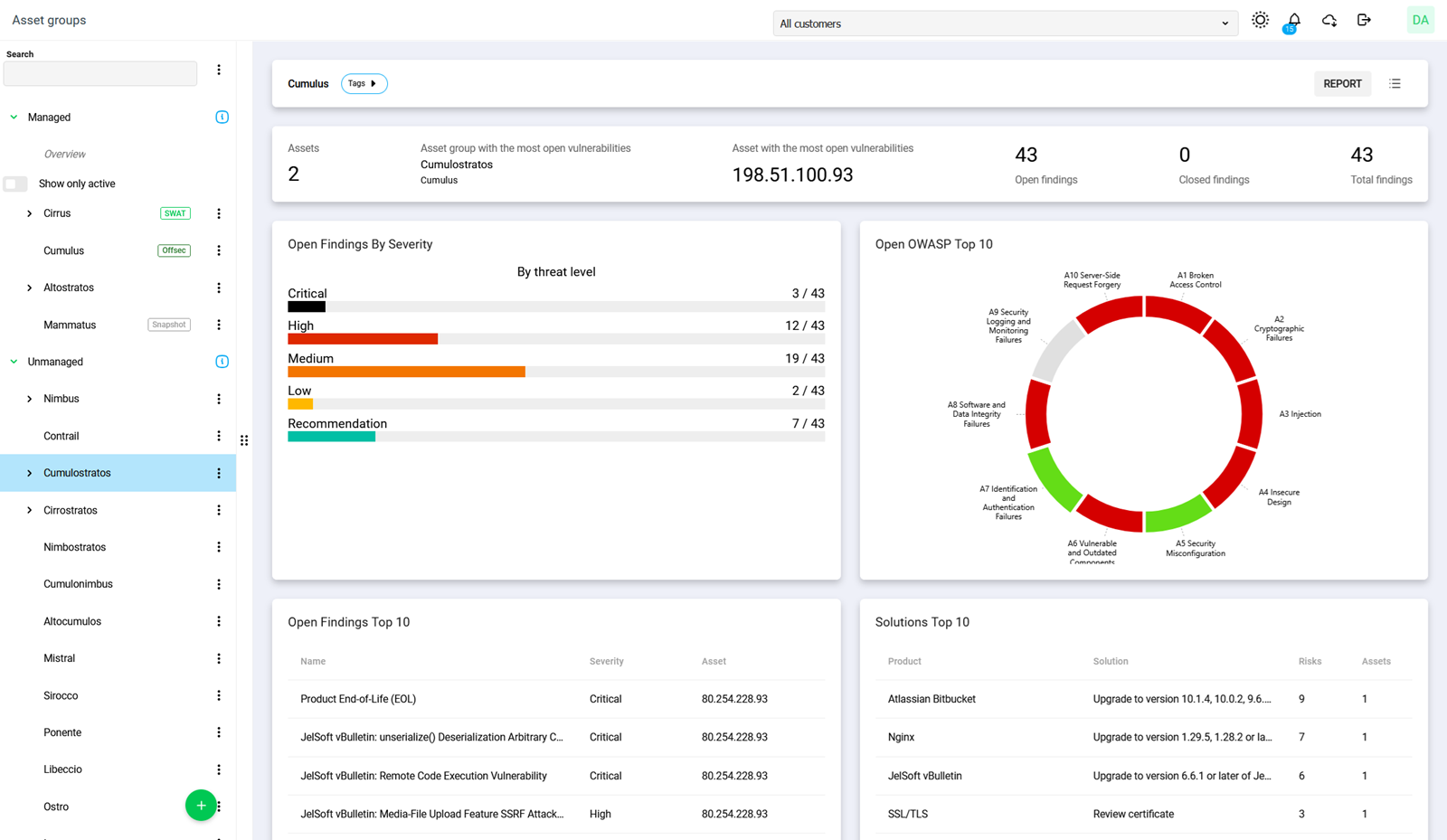
In the Asset groups view, assets are listed under the overview panel of Managed section on the left hand side. Click and drag the border to resize the panel.
Asset groups listed under Managed are maintained by Outpost24 and are not editable, while asset groups listed under Unmanaged can be edited by your organization.
Each card is a graphical representation of number of open findings, fixed findings, remediated findings, a graphical representation of the CVSSv3 score and a graph showing the trends of the findings.
Overview
Clicking the Asset groups overview tree column to the left shows the overview bar at the top is the combined data for all instances.
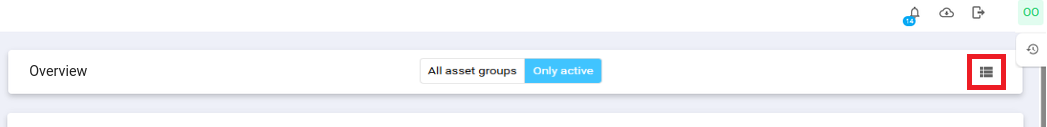
The All asset groups - Only active button filters data for all the cards in this view:
-
All asset groups – shows data from all Managed Asset Groups, even those without active subscriptions (default).
-
Only Active – shows data only from assets and asset groups with active subscriptions.
Selecting a managed group changes the top tool bar displaying information about the asset group and buttons for generating a summary or reports as well as the toggle for the list- and dashboard view.
Clicking on Assets, Most open vulnerable asset group, Most open vulnerable asset, Open Findings, and Closed Findings opens a filtered view in Asset or Findings for each of the items respectively.
Assets
Show the total number of assets associated with all of the Asset Groups. If an Asset Group is selected, then the value represents the assets associated with selected Asset Group. Assets are groupings of one or several identifiers such as IP addresses and host names that represent distinct resources customers wants to secure. As such, an asset may represent entities such as employee's, websites, databases, OCI images, cloud resources, Outpost24 agents etc.
See Assets for more information.
Asset Group with the Most Open Vulnerabilities
Shows the asset group with the most open findings and the asset group it belongs to if it is of Managed type. Clicking on it displays a filtered view with the affected parent group or asset group and the associated assets are listed together with the findings
Asset with the Most Open Vulnerabilities
Shows the asset with the most open findings. As Outpost24 services scan and analyze targets, findings are generated and associated with the corresponding assets.
See Assets for more information.
Open Findings
Number of open findings.
An open finding is defined as a finding with the status set to PRESENT, PENDING VERIFICATION, or IRREPRODUCIBLE.
Findings are the potential risks and recommended reconfiguration suggestions found during automatic and manual assessments of the target asset. These vary from security best practices which lower the attack surface of the target to exploitable vulnerabilities that were verified and confirmed as being present and relevant for the target.
Findings include their classification, risk score and information describing what it is, why it was found and how an attacker might be able to exploit the vulnerability as well as provide clear solutions to remediate the risk.
See Vulnerabilities for more information.
Closed Findings
Number of closed findings.
A closed finding is defined as a finding with a non-empty value of its fixed attribute.
See Vulnerabilities for more information.
Total Findings
Total number of findings in all asset groups.
See Vulnerabilities for more information.
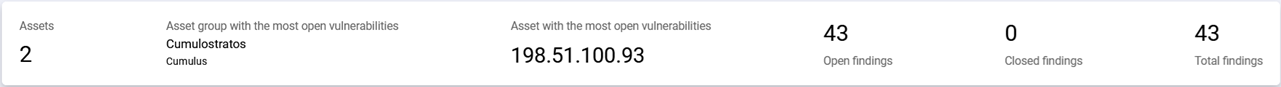
Findings by Severity
This card displays a breakdown of all open vulnerabilities organized by severity level. Each severity category (Critical, High, Medium, Low, and Recommendation) shows a visual bar representing the proportion of vulnerabilities in that category, along with the count relative to the total number of vulnerabilities.
See Vulnerabilities for more information.
Clicking on any of the severity bars redirects you to a filtered view of findings of the selected score level.
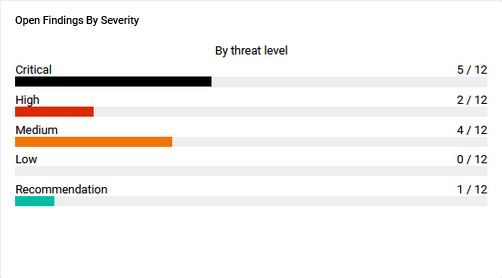
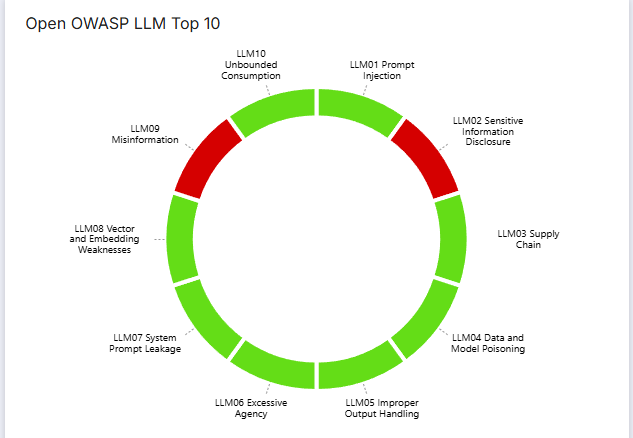
Open OWASP Top 10
The Open OWASP Top 10 card display the findings in a graphical format according to the score of the vulnerability according to OWASP. The Open Worldwide Application Security Project (OWASP) Top 10 is a standard awareness document for developers and web application security, and represents a broad consensus about what the most critical asset group security flaws are.

Clicking on the various colored parts of the OWASP diagram redirects you to a filtered list in the Findings Vulnerability view.
This diagram will only be displayed if at least one asset is of Appsec type identified by the source being any of SCALE, SCALE_API, SCALE_SPA, APPSEC, SWAT, ASSURE or SNAPSHOT.
Open OWASP Mobile Top 10
The Open OWASP Mobile Top 10 card presents findings in a graphical format according to the severity score of vulnerabilities identified in mobile applications, following OWASP guidelines. The OWASP Mobile Top 10 is a standard awareness document for mobile application security and highlights the most critical risks impacting mobile apps. It reflects a broad industry consensus on common mobile security flaws, enabling teams to better understand, assess, and mitigate security risks across mobile platforms.

Open OWASP API Top 10
The Open OWASP API Top 10 card displays findings in a graphical format based on the severity score of API-related vulnerabilities, aligned with OWASP standards. The OWASP API Top 10 is a standard awareness document focused on the most critical security risks affecting Application Programming Interfaces (APIs). It represents a broad consensus from the security community on common and high-impact API security weaknesses, helping organizations identify, prioritize, and remediate risks in API-driven architectures.
Open OWASP LLM Top 10
The Open OWASP LLM Top 10 card presents findings in a graphical format based on the severity of vulnerabilities identified in systems that use large language models. The OWASP LLM Top 10 highlights the most common and impactful risks specific to LLM-powered applications, such as prompt injection, data leakage, and model misuse.
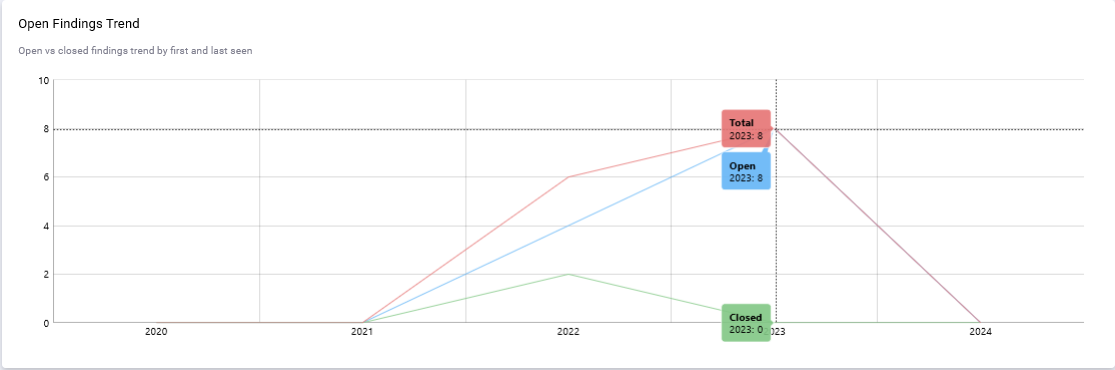
Open Findings Trend
This metric provides a comprehensive view of how business risks are evolving over time tracking the lifecycle of open and closed findings from the moment they are first identified (First seen) to when they no longer appear (Last seen). By analyzing this trend, valuable insights can be gained into the effectiveness of your risk management strategies and identify areas that require attention or improvement.
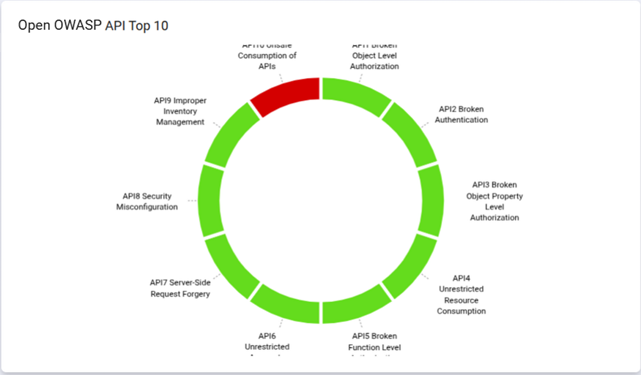
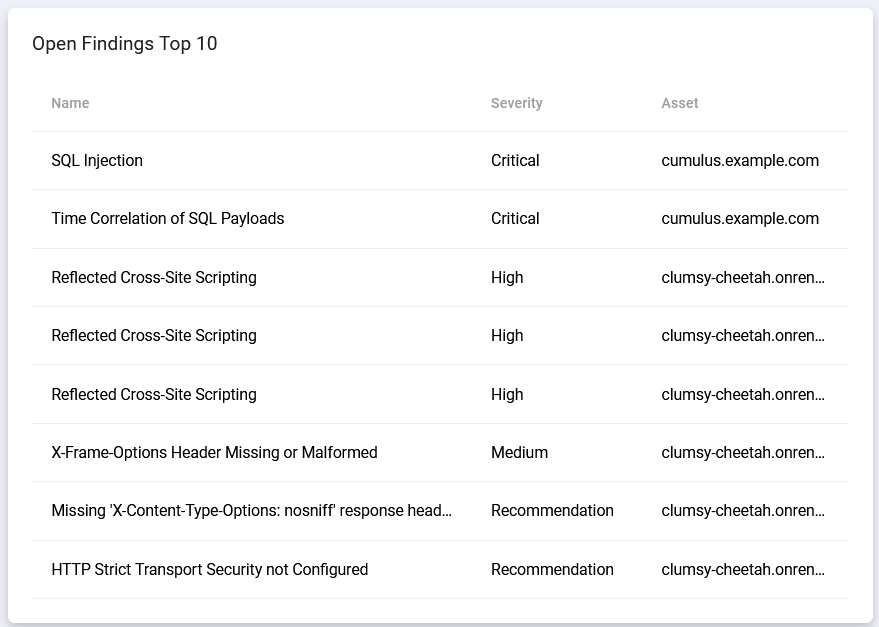
Open Findings Top 10
Open Findings Top 10 shows ten most recent, still open findings with the highest CVSS severity along with the severity and asset they were detected on.
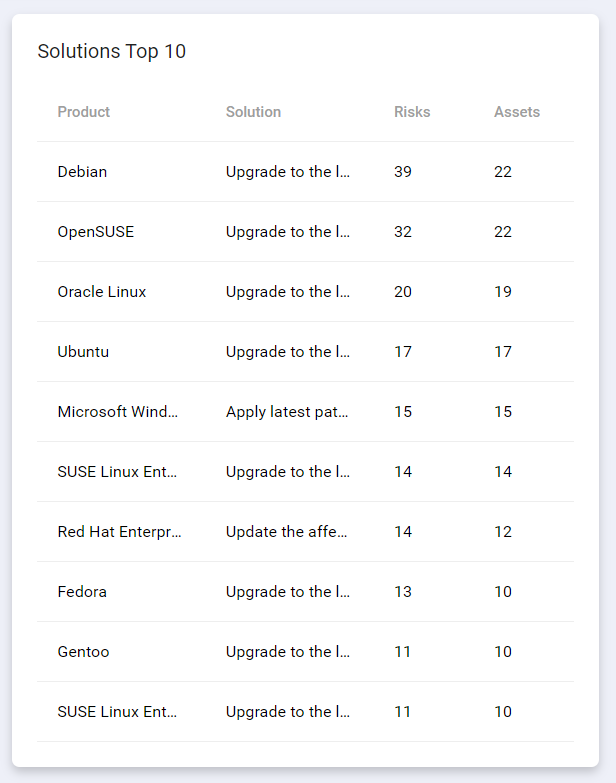
Solutions Top 10
Solutions Top 10 shows ten actions that will resolve most vulnerabilities along with the number of risks and affected assets in unmanaged asset groups.
Subscriptions
The Subscriptions card represents the customer's engagement with Outpost24 and each entry corresponds to an already purchased and paid subscription.
The Subscription card list the current subscriptions assigned to the selected asset group, as well as those that are unassigned and a history of all of them.
The Subscription list can be exported to a CSV file by clicking the export icon ![]()
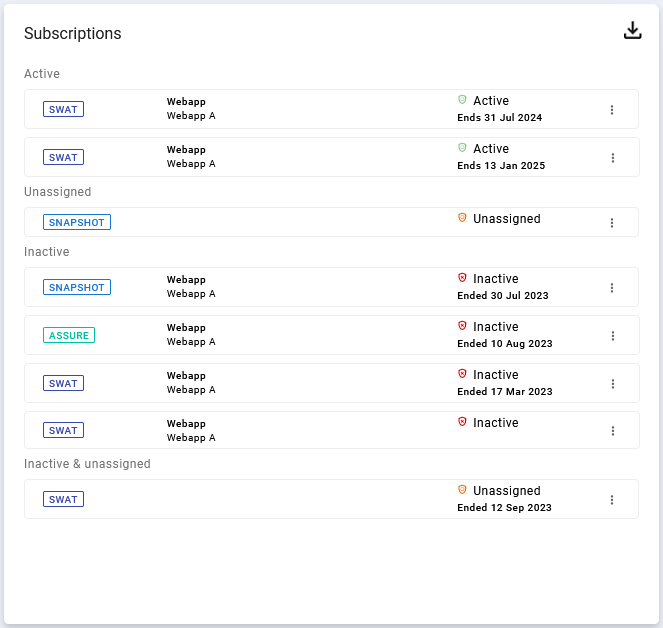
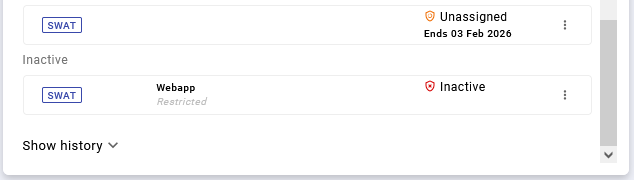
The list in the Subscription card is sorted into four groups: Active, Unassigned, Inactive, and Inactive & unassigned.
|
Subscription Status |
Description |
|---|---|
|
|
Active show the subscriptions that are currently active and are more than 30 days away from expiring. |
|
|
Ending soon shows an active subscription where the end date is less than 30 days from expiring giving you a warning that the subscription is on the end of its valid period. |
|
|
Unassigned to any asset group but active until date. |
|
|
Inactive show subscription where the subscription time has expired, or subscriptions that have an activation date in the future. |
There are cases where licenses expire without having been used. These are listed under Inactive & unassigned at the bottom.
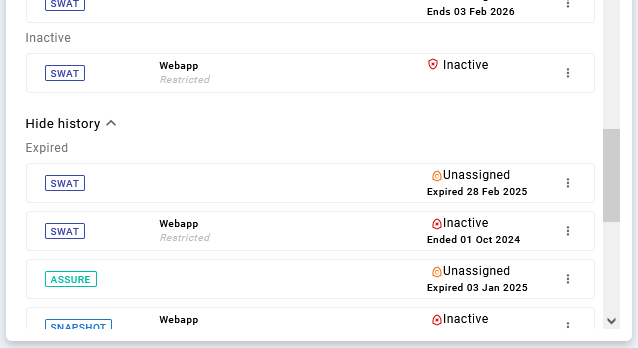
Historical Data is hidden under the Show history dropdown and show the expired subscriptions.
Request Verification of Findings
The subscription types Offsec and Verification determine how penetration testing results are managed and whether findings can be verified after remediation.
-
OffSec subscription: Provides penetration tests on your asset groups and generates findings with remediation suggestions.
-
Verification subscription: Provides all of the above, plus the ability to request verification of findings after you have applied remediations.
The option Request Verification is not available under the OffSec subscription.
Verification ensures that Outpost24 re-tests previously identified findings to confirm that they have been successfully resolved.
The Verification confirms that the remediation actions are effective, and reduces the risk of recurring vulnerabilities. It also provides documented assurance for compliance or internal reporting. If your organization requires validation that security findings have been fixed, the Verification subscription is essential.
Steps to Request Verification
-
In the Outpost24 portal, navigate to the findings you want to review.
-
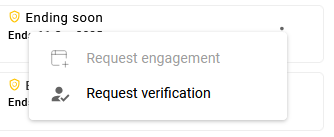
Open the context menu by clicking the three dots (⋮) at the end of the findings row.
-
If your subscription type is Verification, the option Request Verification is displayed.
-
-
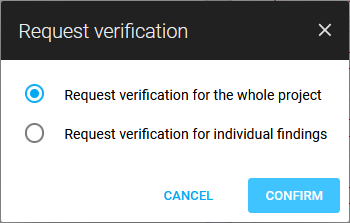
Choose your verification scope by clicking Request verification; two choices are displayed:
-
Request Verification for the whole project - This triggers a verification for all findings across all asset groups linked to the selected subscription.
-
Request Verification for individual findings - Opens a pre-filtered view of the subscription’s asset groups, allowing you to manually select findings to verify.
-
-
To submit the request, click the blue CONFIRM button to initiate verification.
Outpost24 will re-test the selected findings and update the findings list with the verification results. You can then review which issues are confirmed as fixed and which may require additional action.
Overview Cards
The Overview Card shows each Asset group with basic information and breaks down the results in to six categories. The results can be filtered by toggling the Show only vulnerable and Show only active subscription switches
The Show only vulnerable switch, when activated, exclude recommendation findings from being counted and only count findings containing vulnerabilities.
The Show only active subscription switch filters out all but active subscriptions, and show only asset groups that currently have an active subscription attached to it, as well as information about said and past subscriptions in the Overview cards.
|
Card Info |
Description |
|---|---|
|
Findings |
The total number of Findings, regardless of their status. |
|
Open Findings |
Total number of open findings. |
|
Closed Findings |
Total number of closed findings. |
|
Assets |
Total number of assets. |
|
Critical Findings |
Total number of findings with Critical severity. |
|
High Findings |
Total number of findings with High severity. |
Clicking on the name of the asset group opens the dashboard for said asset group, whereas clicking on the different info sections will redirect you to a filtered list of findings.
The Overview Card is only available for Managed type of group.
Table View
To toggle from Dashboard view to a Table view, click the list icon ![]()
The table view operates like every other table views in the portal with basic CRUD operations such as filtering, adding/removing columns, and using view templates with view templates panel.
Clicking on an Asset group open the details. The details view of an unmanaged Asset group only contains two tabs:
-
Details
-
Comments
A Managed Asset group details view has six tabs:
-
Details
-
Subscriptions
-
Credentials
-
Summaries
-
Activity Log
-
Comments
|
Option |
Format |
Description |
|---|---|---|
|
Active subscription |
|
The Active subscription column indicates whether the asset has one or more currently active subscriptions or if it is inactive. |
|
Asset group ID |
|
Clickable asset group IDs where this asset is assigned. Clicking an ID opens the Asset Groups view with that group selected. |
|
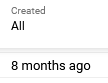
Created |
|
Number of days since the Asset group was created. |
|
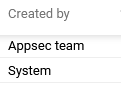
Created by |
|
Who created the Asset group:
|
|
Dynamic |
|
Indicates if the Asset group is Dynamic or not. A Dynamic Asset Group is managed by the system, so that all assets matching the criteria for the group is automatically added to the group. Assets that no longer match the criteria is removed. For more information about Dynamic Asset Groups, see Dynamic Asset Groups. |
|
Excluded asset tags |
|
See Tags section. |
|
ID |
|
Unique identifier of the asset. |
|
Included asset tags |
|
See Tags section. |
|
Managed |
|
Managed asset groups are maintained by Outpost24 and are not editable. Unmanaged asset groups are editable by your organization. |
|
Name |
|
Name of the asset group |
|
Parent ID |
|
Display the parent asset group ID |
|
Path |
|
Show the ID of parent asset group if exists and the ID of current asset group. |
|
Source |
|
Which source scanner or product type does the asset groups originate from. Can only be set by Outpost24 for managed asset groups at the moment. |
|
Summary ID |
|
Show the ID of the current summary of asset group. |
|
Summary Published |
|
Show the published date of the current summary of asset group. |
|
Tags |
|
Displays the available tags associated with the group. See Tags article for further information about tags. |
|
Type |
|
Indicates the category of a Asset group. |
|
Updated |

|
Timestamp of when the asset was last updated at all for any reason, system- or user-initiated. |
|
Updated by |
|
Who did the last updating action, system, user, or AppSec team and so on. |
Tags
Right clicking on an Asset group in the table view opens the context menu providing tools to configure the handling of the tags.
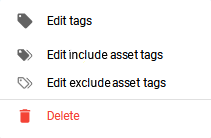
-
Edit tags - Lets you create the tags of the product. See Tags article for further information about tags.
-
Edit include assets tags - Lets you configure which assets to include depending on their tags. Specify tags ,for example,
team:support,location:karlskronathat the assets must match to be included. Multiple tags are combined with an AND operator. -
Edit exclude assets tags - Lets you configure which assets to exclude depending on their tags. Specify tags, for example,
team:internalit,location:karlskronato exclude assets. Multiple exclude tags are combined with an OR operator.
Detailed View Tabs
Details tab
The Details tab is displayed for both Unmanaged- and Managed asset groups.
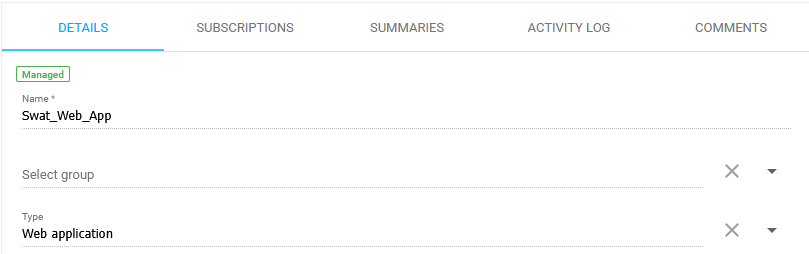
Name: Name of the asset group.
Select Group: Name of the parent asset group.
Type: What type of asset group is it?
-
Web application
-
Instance
-
API
-
Internal
-
External
-
Mobile
-
Physical
-
Wireless
-
Phishing
-
Red
-
Assumed
-
Digital
-
Hardware
-
Project
Subscription tab
The Subscriptions tab is displayed only for Managed asset groups, and list all the associated subscriptions to the asset group.
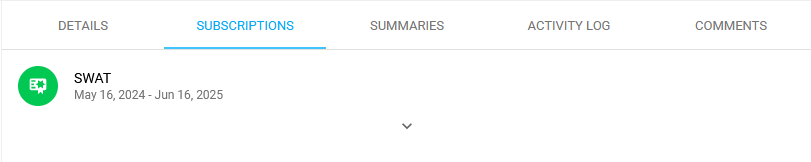
For more information about subscriptions, see Subscriptions Overview
Credentials tab
The Credentials tab is displayed only for Managed asset groups, and lists all credentials associated with the currently selected asset group.
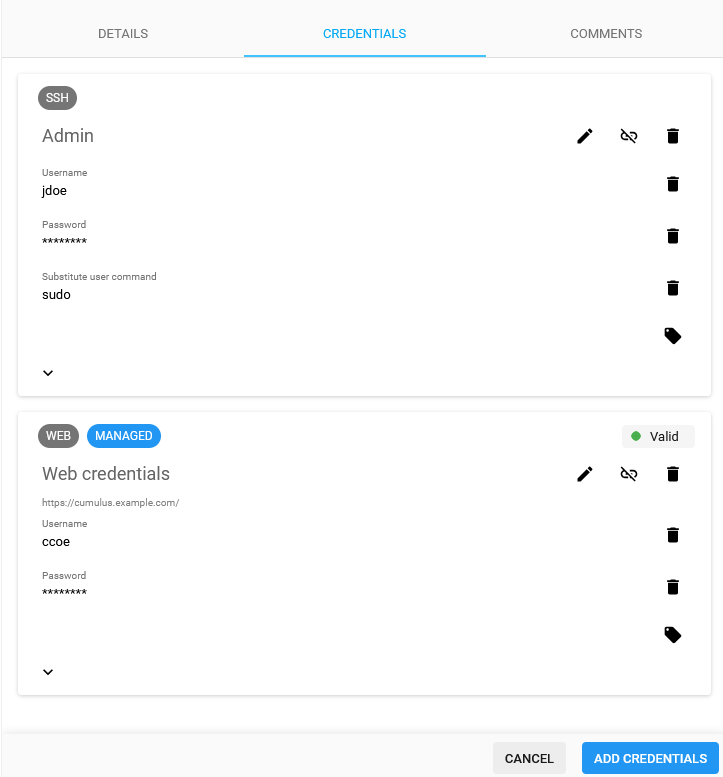
Within the Credentials tab, you can:
-
Add credentials to the asset group.
-
Edit existing credentials.
-
Remove credentials from the selected Asset Group using the Unlink button.
Managed vs. Unmanaged Credentials
When working with Managed credentials note that:
-
Credentials marked as Managed are controlled and accessible by Ghostlab.
-
only Ghostlab personal can unlink credentials from a managed asset group.
-
only Managed credentials can be linked to managed asset groups.
-
Credentials created outside of Ghostlab (unmanaged) can be freely edited or deleted by the user.
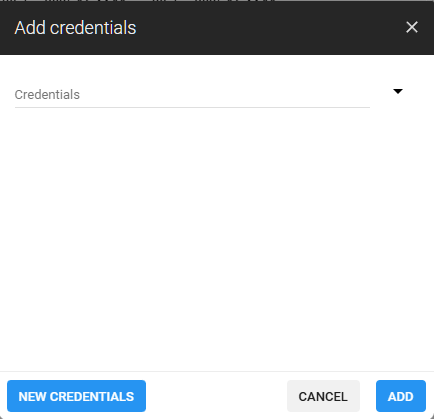
Adding Credentials
When adding credentials to an asset group, you may select from Existing credentials, or Create new credentials directly within the Credentials tab view.
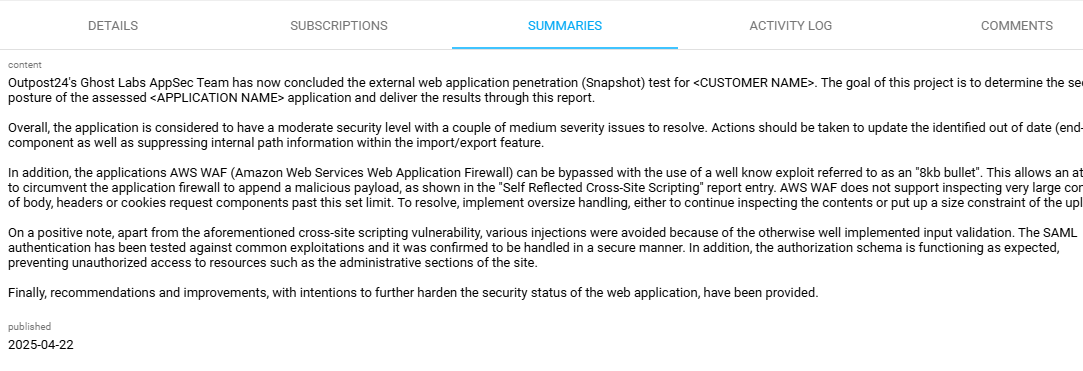
Summaries tab
The Summaries tab is only displayed for Managed asset group and outlines the results of a web application penetration test. For more information, see the Summary section in this article.
Comments tab
The Comments tab is displayed for both Unmanaged- and Managed Asset Groups.
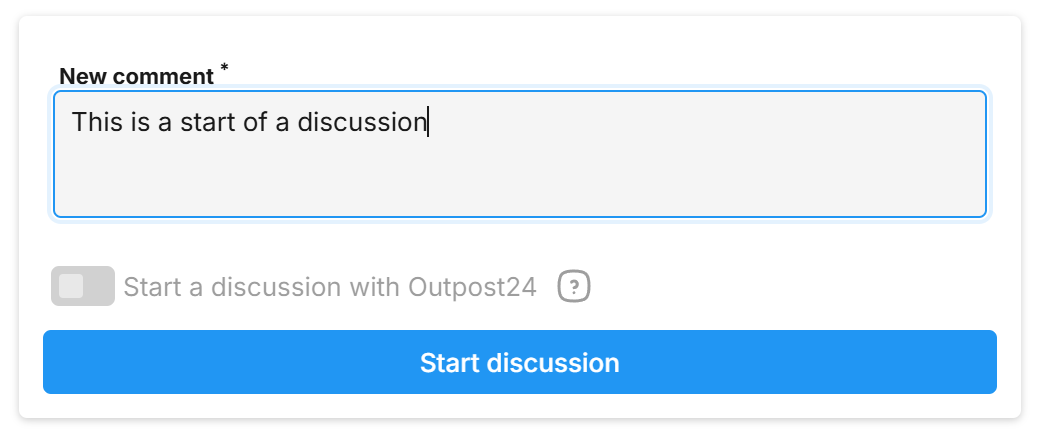
In the Comments tab you can start a discussion with Outpost24 Appsec team about. Discussions are normally customer-internal. Only when eligible (via associated subscription) may a dialog between customer and the Outpost24 AppSec team be initiated.
For more information about comments, see Discussions and Commenting.
Manage Asset Groups
Create an Asset Group
To create a Asset Group:
-
Navigate to the Asset group management interface in the Portal.
-
Click the green plus
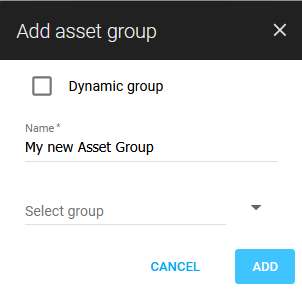
c
-
Enter a name for the Asset Group.
-
Use Select group if you want to create a nestled group, else leave it blank which will create a main group.
-
Click ADD to save the group.
-
The created Asset Group is presented under the Unmanaged collapsible block.
-
Click on the Asset Group’s name to view its details about the group.
Populating an Asset Group
To add assets to the Asset Group:
-
Navigate to Assets in the Main Menu.
-
Right click on the asset you want to add to the Asset Group to open a context menu.
-
Select Manage asset groups to open the Manage asset group form.
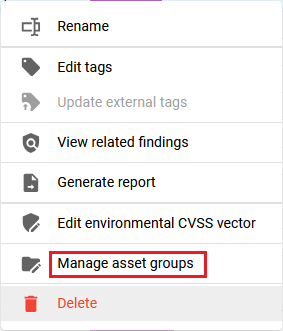
-
Select the group to which you want to add the asset.
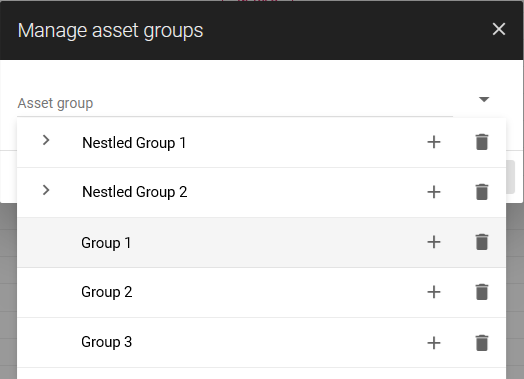
-
Click Save.
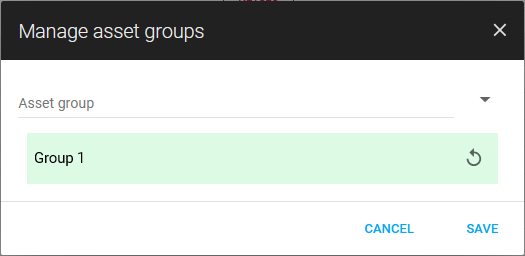
-
Return to the Asset Group view and select the Asset Group you created which is now populated.
Renaming an Asset Group
To rename an Asset Group:
-
Navigate to the Asset group management interface in the Portal.
-
Click the kebab

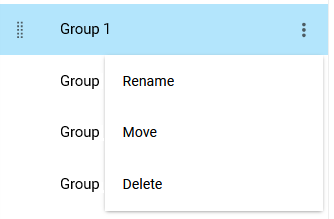
-
Enter a new name for the group.
-
Click Rename.
Moving an Asset Group
To move an Asset Group:
-
Navigate to the Asset group management interface in the Portal.
-
Click the kebab

-
In the drop-down menu select a destination group.
-
Click Move.
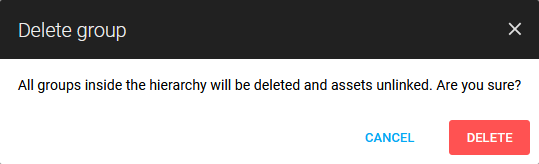
Deleting an Asset Group
To delete an Asset Group:
-
Navigate to the Asset group management interface in the Portal.
-
Click the kebab

-
Click Delete to remove.
Finding an Asset Group
To filter asset groups:
-
Navigate to the Asset group management interface in the Portal.
-
Enter the name of the asset group into the search input.
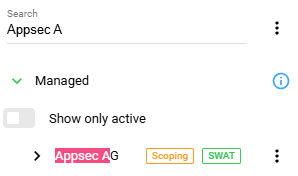
The default filter does not include children asset groups if their names do not match the search value. To change this behaviour:
-
Click the kebab

-
Click Include unmatched subgroups.
Customer Actions
Actions require right clicking a finding to access the context menu
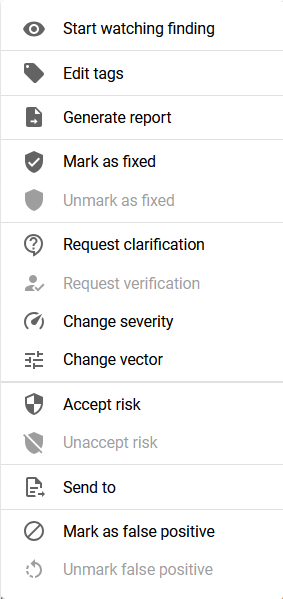
or selecting one or more findings by checking the boxes in the beginning of the row in the Vulnerabilities view to toggle the action bar on the bottom.
Accept Risk
If a risk cannot be mitigated right away, that risk can be accepted so that it will not be picked up every time a scan runs.
To accept a risk.
-
Click the Accept Risk

-
Enter a date until when the acceptance should last and a comment.
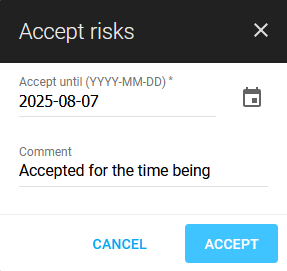
-
Click Accept.
The risk will now be omitted from future scans until the set date.
Request Verification
Findings
For more information about Findings, see Vulnerabilities.
See Filters for common filtering options in the portal.
Tags
By using the Tag ![]()
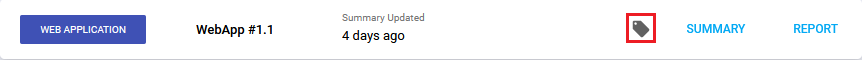
For more information about tags, see Tags.
Summary
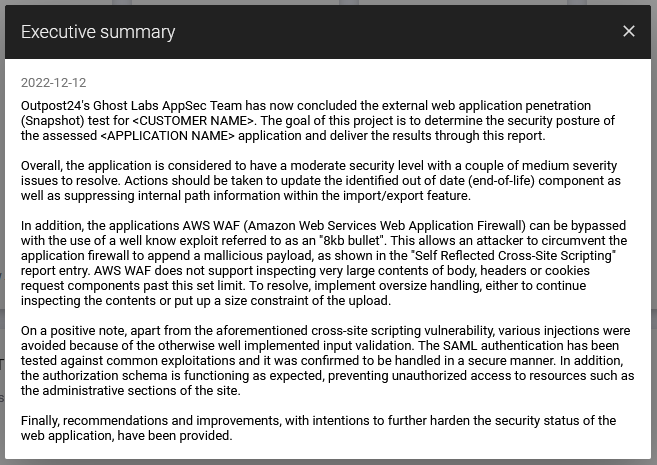
The Executive Summary is a text aimed to describe the overall security level of the application in question. This includes a brief summary of the general security status as well as the identified vulnerabilities.
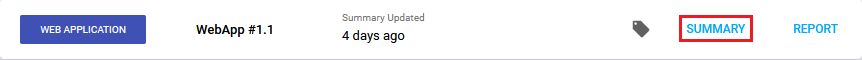
To see the Summary:
Click on Summary button in the upper right corner of the status-bar in the Asset groups dashboard.
The field Summary Updated indicates when the summary was last updated.
Reports
To export reports for asset groups from the Portal UI:
-
Select a asset group.
-
Click on the Report button near top right corner.
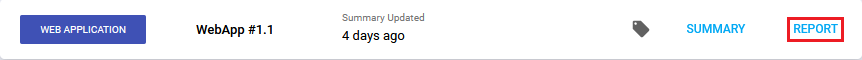
-
The report type options available to choose from are: Vulnerabilities, Solutions and Delta.
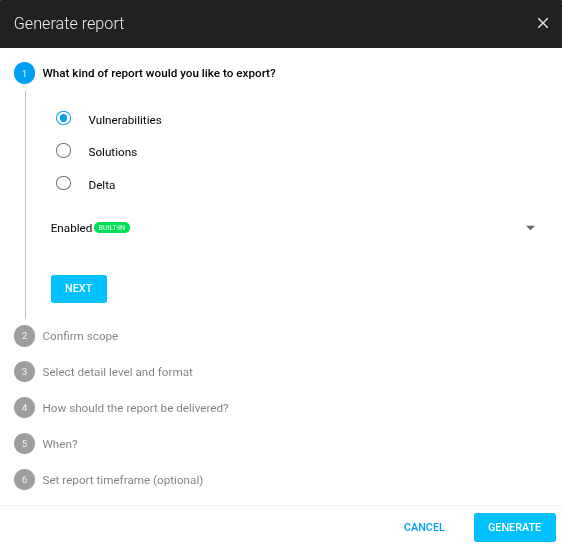
Reports use View Templates to filter the reports by predefined templates. The built-in SWAT template is pre-selected and filters out fixed findings by default.
-
Continue with the same steps as in a normal Report.
For more information, see Reports.
Note that the user who requests the Asset Groups report may only see vulnerabilities and summaries to which they have access privilege. For example, a main user sees everything, but a sub-user with limited privilege will only see reports about the assets that they can access in the asset group.
If all assets or asset groups related to a scheduled report configuration are deleted, the scheduled report configuration will be automatically removed.
Related Articles
- Removing an Agent from Windows
- Discovering the Agent in OUTSCAN
- Installing a Linux Agent
- Check Connectivity to Agent Server
- Checking if Agent is Running
- Agent Installation Introduction
- Automatic Asset Joining With Netsec
- Firewall Setup for Agents
- Engagement Requests
- Agent Call Home
- Asset Discovery
- Using the Agent Info Command
- Removing an Agent from Linux
- Retrieving the Agent UUID
- Finding the Agent Version
