Getting Started with CORE
Purpose
This document describes how to get started with the Outpost24 CORE interface.
Introduction
The CORE is a way to centralize the data from all of our scanners such as NetSec, AppSec, and CloudSec in to one view and also providing a powerful tool to drill down in the data to help identify vulnerabilities in key systems.
Prerequisites
To view the results in Outpost24 CORE, the user needs an exclusive license for CORE along with Netsec, Farsight and/or Appsec licenses.
List of Icons
| Icon | Name | Comment |
|---|---|---|
| Dashboard | Takes you to the default home view. |
| Explore | The Explore Menu lets you navigate to:
|
| Reporting | Report configuration See CORE Reporting for more information. |
| Configure | Configuration menu.
|
| IAM | Identity and Access Management. See CORE IAM for more information. |
| Menu | Account menu which contains:
|
| Dark theme | Switches between Light and Dark theme. |
| Licenses | Direct you to the Third-party licenses page in the portal. The Third-party licenses page is a list of licenses of third-party software that is embedded into the platform. |
| Logout | The Logout button displays a logout window. |
| Filter | Displays the various filter options Appstak, Assets, and Findings. See CORE Filters for more information. |
| Edit | Opens an edit function for the selected object. |
| Delete | Delete selected object. |
| Trend toggle | Toggles the Dashboard to show trends in each card. See Trends in CORE Dashboard document. |
| Trend Time Duration | The drop down menu to the right of the trend toggle switch sets the time duration of the trends shown in the dashboard. |
| Reset Columns | Resets the number of column shown and the order in which they are shown. |
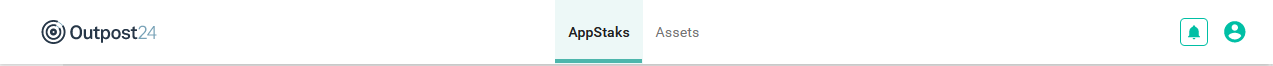
Top Menu
The top menu lets you navigate between the AppStaks tab and Assets tab. To the far right you find the Notifications, the Account menu which contains the Dark theme toggle switch, Licenses and the Logout icon.
AppStaks Tab
AppStaks is groupings of Assets in a way that makes business sense. AppStaks are grouped in to four categories Enterprise, E-commerce, Finance, Accounting, and Uncategorized.
For more information, see CORE AppStaks document.
Assets Tab
Assets are unique hosts provided by the scanners or added automatically while creating a configuration. An asset can also be linked to a group of configurations. One asset can have multiple configurations that are scheduled and scanned independently.
These assets are uniquely defined based on their IP or hostname. Their risk profile in form of top recommended solutions and risk charting provide a quick way of assessing the criticality of an asset, its association with other assets and already performed scans.
For more information, see CORE Assets document.
Account Menu
To the right of the Notification icon is the Account icon which reveals the Account Menu that contains Dark theme, Licenses, and Logout.
Dark Theme
Under the Logout icon is the Dark theme icon which allows you to select between a light or dark background.
Licenses
At the bottom of the menu you find the icon that link you to the Third-party licenses page in the portal. The Third-party licenses page is a list of licenses of third-party software that is embedded into the platform.
Logout
In the menu you find the Logout button. Clicking it displays a logout window where you can select to cancel or logout.
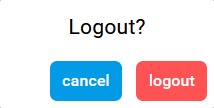
Logging out from the CORE will also log you out from the Portal.
Left Menu
The left side menu lets you navigate between the Dashboard, Explore, Reporting, Configure, and the IAM services.
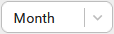
Dashboard
The Dashboard consists of several cards that describes various views of the findings.
Refer to CORE Dashboard document for more information.
Explore
The Explore menu lets you navigate through the various tables.
- AppStak - the AppStaks Tab. See CORE AppStaks to learn more about AppStaks.
- Asset Groups - See CORE Asset Groups to learn more about Assets.
- Assets - the Assets Tab. See CORE Assets to learn more about Assets.
- Findings - the Assets findings. See CORE Findings to learn more about Findings.
Reporting
The Reporting icon takes you to the Report Configuration view where you can configure AppStaks and Assets reports.
Refer to Creating CORE Reports document for more information.
Configure
The Configure icon takes you to the AppStak configuration page where you can create AppStaks, and the Categories configuration page where you can create Categories.
Refer to CORE AppStaks and CORE Configure Categories document for more information.
Identity Access Management
Identity Access Management (IAM) is a service that control access to resources. IAM is used to control who is authenticated (signed in) and authorized (has permissions) to use resources.
Refer to CORE IAM document for more information.
Related Articles
Copyright
© 2024 Outpost24® All rights reserved. This document may only be redistributed unedited and unaltered. This document may be cited and referenced only if clearly crediting Outpost24® and this document as the source. Any other reproduction and redistribution in print or electronically is strictly prohibited without explicit permission.
Trademark
Outpost24® and OUTSCAN™ are trademarks of Outpost24® and its affiliated companies. All other brand names, product names or trademarks belong to their respective owners.