CORE Findings
Purpose
This document describes Findings in the CORE.
Introduction
Findings are the potential risks and recommended reconfiguration suggestions found during automatic and manual assessments of the target asset. These vary from security best practices which lower the attack surface of the target to exploitable vulnerabilities that were verified and confirmed as being present and relevant for the target.
Findings include their risk classification, risk score and information describing what it is, why it was found and how an attacker might be able to exploit the vulnerability as well as provide clear solutions to remediate the risk.
Accessing Findings
By clicking the Explore icon in the menu on the left hand side and selecting findings, an unfiltered list of vulnerabilities is displayed together with the Overall Risk card.

| Column | Description |
|---|---|
| Age * | Number of days since the findings are detected. |
| Asset UUID | The unique identifier of the Asset the Finding belongs to. |
| CVSS V3 | CVSS V3 score range.
|
| CVSS V3 Severity | CVSS V3 severity in qualitative ratings.
|
| Last Scan | The date of the last scan. |
| Farsight Score * | Vulnerability score ranging from 0-100 according to Farsight. |
| First Seen | Date and time when the finding has been seen for the first time. |
| Grade * | Risk level on a scale from A to F where F represents the most critical risks. An Asset's risk is calculated based on:
|
| Last Seen * | Date and time when the finding has been seen last time. The date is set after the scan is finished if the finding is still detected. |
| Name * | Name of the vulnerability. |
| Port | The IP communication port. |
| Protocol | TCP, UDP, ICMP, IGMP or GENERIC. |
| Status | Indicates the different statuses for a finding. Can be marked as:
|
| UUID | The unique identifier of the Finding. |
*) Columns shown by default
By clicking and marking a vulnerability in the list, more information about the vulnerability is displayed in a card on the right hand side.
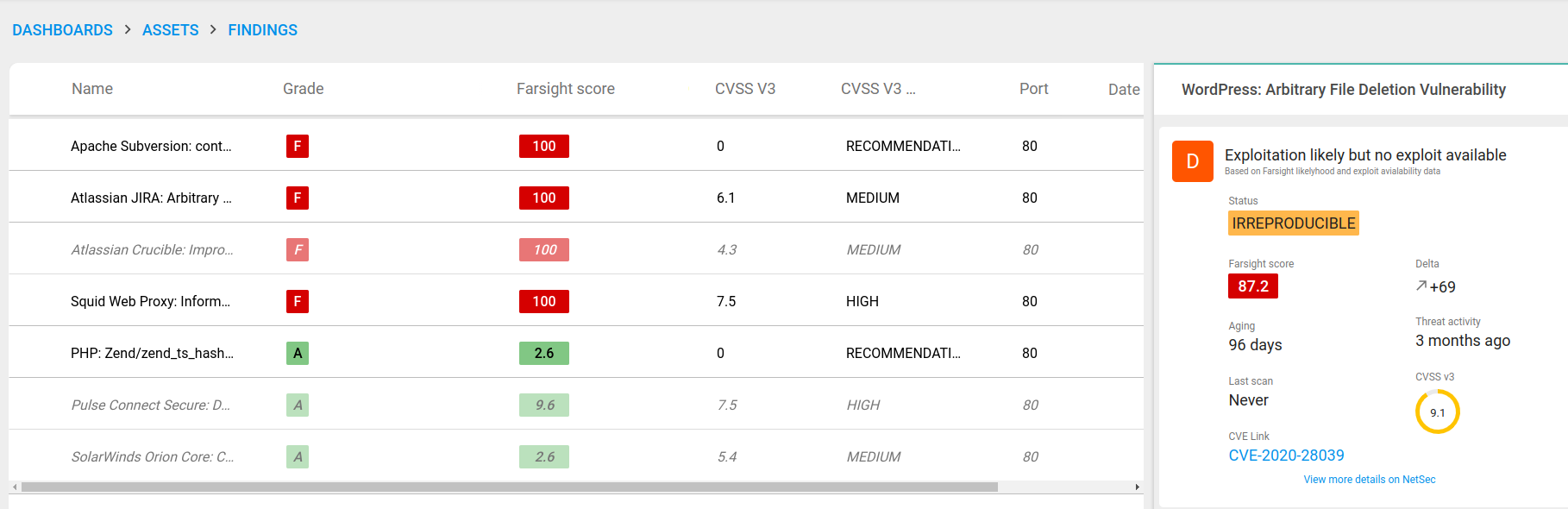
Italic and dimmed rows indicates the finding status to be "closed" on FIXED, ACCEPTED or FALSE_POSITIVE status.
Details
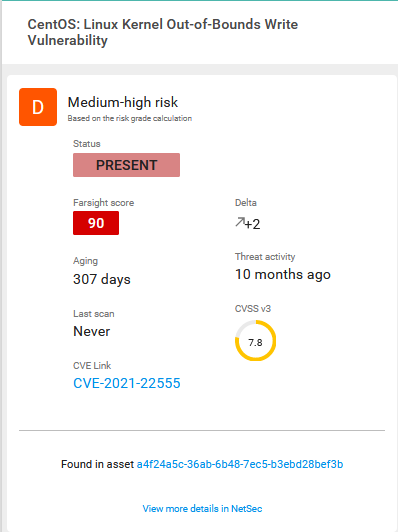
Selecting a Finding in the table displays a detailed report on the specific finding.
| Option | Description |
|---|---|
| Grade | Risk level on a scale from A to F where F represents the most critical risks. An Asset's risk is calculated based on:
|
| Status | Indicates the different statuses for a finding. Can be marked as:
|
| Farsight Score | Score of the vulnerability according to Farsight. |
| Aging | Days since first discovered. |
| Last Scan | When was the last scan performed. |
| CVE-Link | Further information about the vulnerability from the National Vulnerability Database. |
| Delta | Is the difference between the current and the former likelihood values. |
| Threat Activity | When was the threat active. |
| CVSS v3 | CVSS score range.
|
Further details can be access in Vulnerability Management (Netsec) by clicking the View more details on Netsec link at the bottom of the frame.
Multi Select
When selecting more than one row using the check boxes, an average risk value for selected rows is displayed in the card to the right with the number of selected items at the top.

Configuring the Columns
The Columns can be configured in several ways. Columns can be added and removed and the order in which they are displayed can be changed.
Changing Column Width
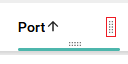
All the columns are configurable in width by dragging the dotted area on the right side of the column head.
Changing Column Presentation
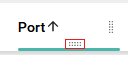
By dragging the dotted area on bottom of the column head, the order in which the columns are presented can be changed.
Selecting Columns
By clicking on the + sign in the upper right corner in the column head row, a column menu is displayed where columns can be selected and deselected to configure the findings view.

The content in the column menu may change depending on which view it is opened in.
Reset To Default
- To reset to default column presentation, press the Reset icon.
- A confirmation box is displayed, click the red Reset button to confirm.
- This resets the number of column shown and the order in which they are shown to default.
Farsight
The Farsight feature is a powerful tool that helps organizations address potential vulnerabilities in a more effective manner, regardless of the CVSS score or the existence of an exploit. With this feature, organizations can focus on mitigating vulnerabilities that are most relevant and potentially impactful, based on the prediction of an increased risk as determined by Farsight's advanced algorithm.
The traditional approach to vulnerability management involves focusing on the CVSS score, which provides a numerical representation of the severity of a vulnerability. However, this method has several limitations, including the fact that it does not take into account the likelihood of a vulnerability being exploited. The Farsight feature considers threat actors, their tools and campaigns as well as the historical record of exploitation including usage of malware to provide a more comprehensive assessment of the risk associated with a vulnerability.
By using Farsight, organizations can prioritize their efforts to address the vulnerabilities that are most likely to cause harm. This not only saves time and resources, but also helps organizations stay ahead of potential threats and maintain a secure environment for their critical assets. Moreover, the model that powers the Farsight feature is constantly adapting to new information, ensuring that organizations are always getting the most up-to-date and accurate risk assessments.
Risk classification of assets and services serves a purpose and should be conducted to further distinguish where to focus most efforts. This task can be time-consuming and may not produce viable results in the first couple of iterations. Farsight enables you to filter out some unlikely vulnerabilities with little to no prior knowledge about the vulnerabilities or assets, getting you on track with your vulnerability program faster.
Farsight score
Farsight score is a risk indicator that shows how likely a vulnerability is to be exploited compared to average, where approximately 95% of all vulnerabilities are never exploited. The score ranges from 1 to 100, with a score of 100 indicating that the vulnerability is highly likely to be exploited in the wild within the next 12 months. The benefit to the customer is the ability to drive more aggressive risk-based remediation, focusing on even fewer vulnerabilities that reach a particular likelihood. Any vulnerability that has already been exploited in the wild will get a risk value of 100.
Since risk score is constantly adapting to new information, the risk rating can decrease as well as increase based on activity in the wild.
Prerequisites
To use Farsight you need the function enabled in your subscription. Contact support for more information on how you can enable the Farsight function.
Farsight in CORE
In the CORE, Farsight is a key component in the risk grade of Findings, Assets, Asset Groups, and AppStaks where it is represented by an A-to-F scale. In addition to the letter grade, the numerical representation of the Farsight score is displayed as a Farsight score in the Findings view, providing a more detailed and specific understanding of the level of risk.
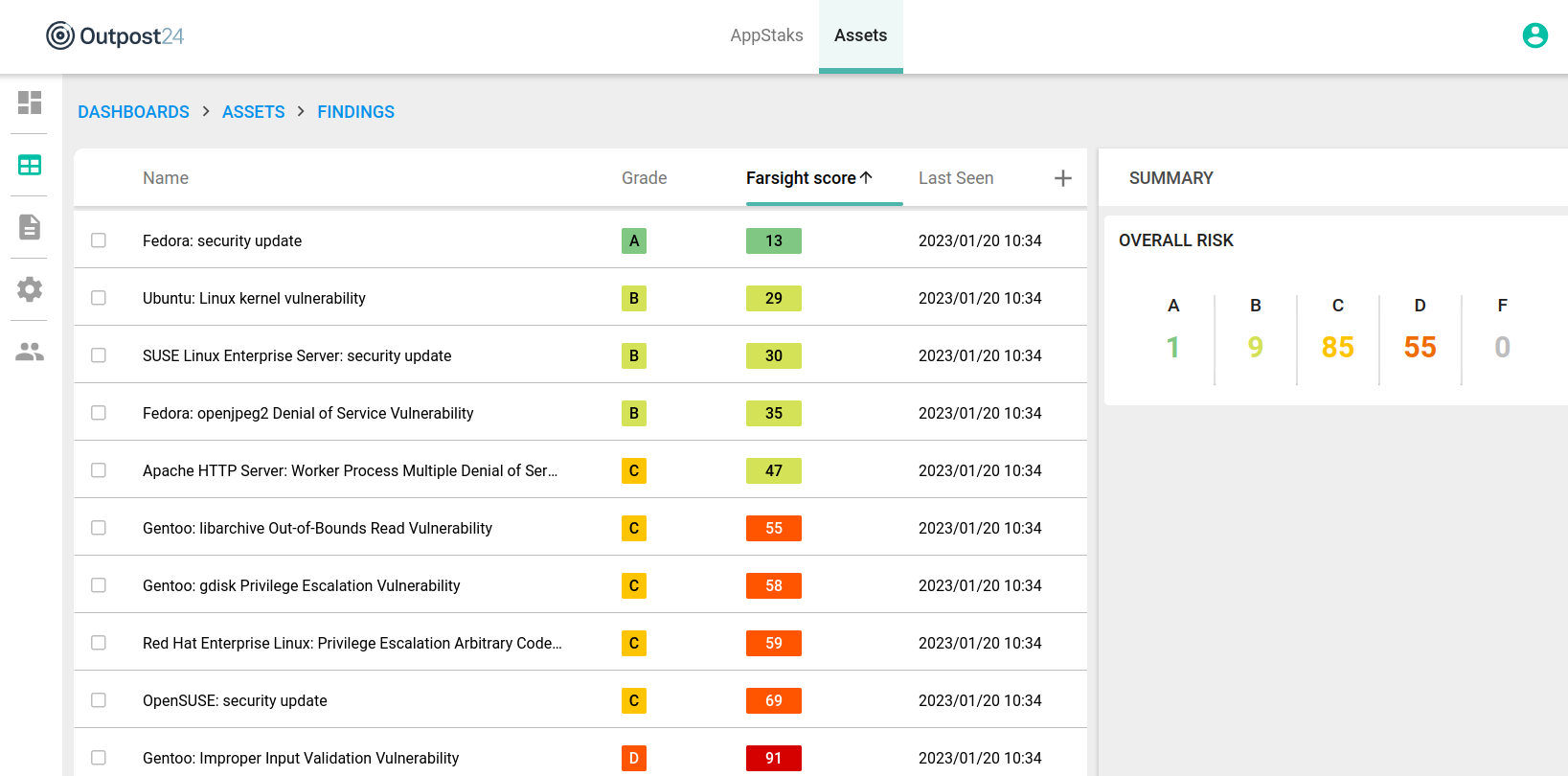
Clicking the Findings tab takes you to the findings view, where the findings are listed.
Selecting a finding displays a more detailed view in the panel to the right.

| Option | Description |
|---|---|
| Age * | Shows how old the vulnerability is. |
| Asset UUID | The unique identifier of the Asset the Finding belongs to. |
| CVSS V3 | CVSS V3 score range.
|
| CVSS V3 severity | CVSS V3 severity in qualitative ratings.
|
| Last Scan | The date of the last scan. |
| Farsight score * | Risk indicator that shows how much more likely a vulnerability is to be exploited compared to average. The risk indicator present the likelihood values in an 1-100 format. |
| First Seen | Date and time when the finding has been seen for the first time. |
| Grade * | Risk level on a scale from A to F where F represents the most critical risks. The following metrics are used and evaluated when calculating the risk level in the following order:
This order works as a funnel in a falling order. |
| Last Seen * | Last time date when threat activity has been detected by the scanner. |
| Name * | Vulnerability name |
| Port | The IP communication port. |
| Protocol | TCP, UDP, ICMP, IGMP or GENERIC |
| Status * | Indicates the different statuses for a finding. Can be marked as:
|
| UUID | The unique identifier of the finding. |
*) Columns shown by default
| Option | Description |
|---|---|
| Status | Indicates the different statuses for a finding. Can be marked as:
|
| Farsight score | Risk indicator that shows how much more likely a vulnerability is to be exploited compared to average. The risk indicator present the likelihood values in an 1-100 format. |
Delta | Is the difference between the current and the former likelihood values. |
| Aging | Days since first discovered. |
| Threat activity | Last time date when threat activity has been detected by the watcher community. |
| Last Seen | Last time date when threat activity has been detected by the scanner. |
| CVSS v3 | CVSS V3 score range.
|
| CVE Link | Further information about the vulnerability from the National Vulnerability Database. |
Only findings that has the status PRESENT are included when calculating the grades for Assets, Asset Groups, and AppStaks.
Related Articles
Copyright © 2024 Outpost24® All rights reserved. This document may only be redistributed unedited and unaltered. This document may be cited and referenced only if clearly crediting Outpost24® and this document as the source. Any other reproduction and redistribution in print or electronically is strictly prohibited without explicit permission. Trademark Outpost24® and OUTSCAN™ are trademarks of Outpost24® and its affiliated companies. All other brand names, product names or trademarks belong to their respective owners.
