Last updated: 2026-02-26
Purpose
This article describes how to create Amazon Web Services (AWS) credentials.
Introduction
Amazon Web Services (AWS) is a cloud computing platform that enables organizations to build and operate digital systems in the cloud without maintaining physical servers. The Generate AWS Credentials feature guides users through creating secure Identity and Access Management (IAM) credentials, such as access keys or IAM roles, so the platform can interact safely with their AWS accounts. By configuring precise IAM policies, users ensure that Outscan gains the necessary permissions to discover and scan AWS resources without granting excessive access. This approach enhances both visibility and control within the cloud security workflow.
Create an IAM Policy
-
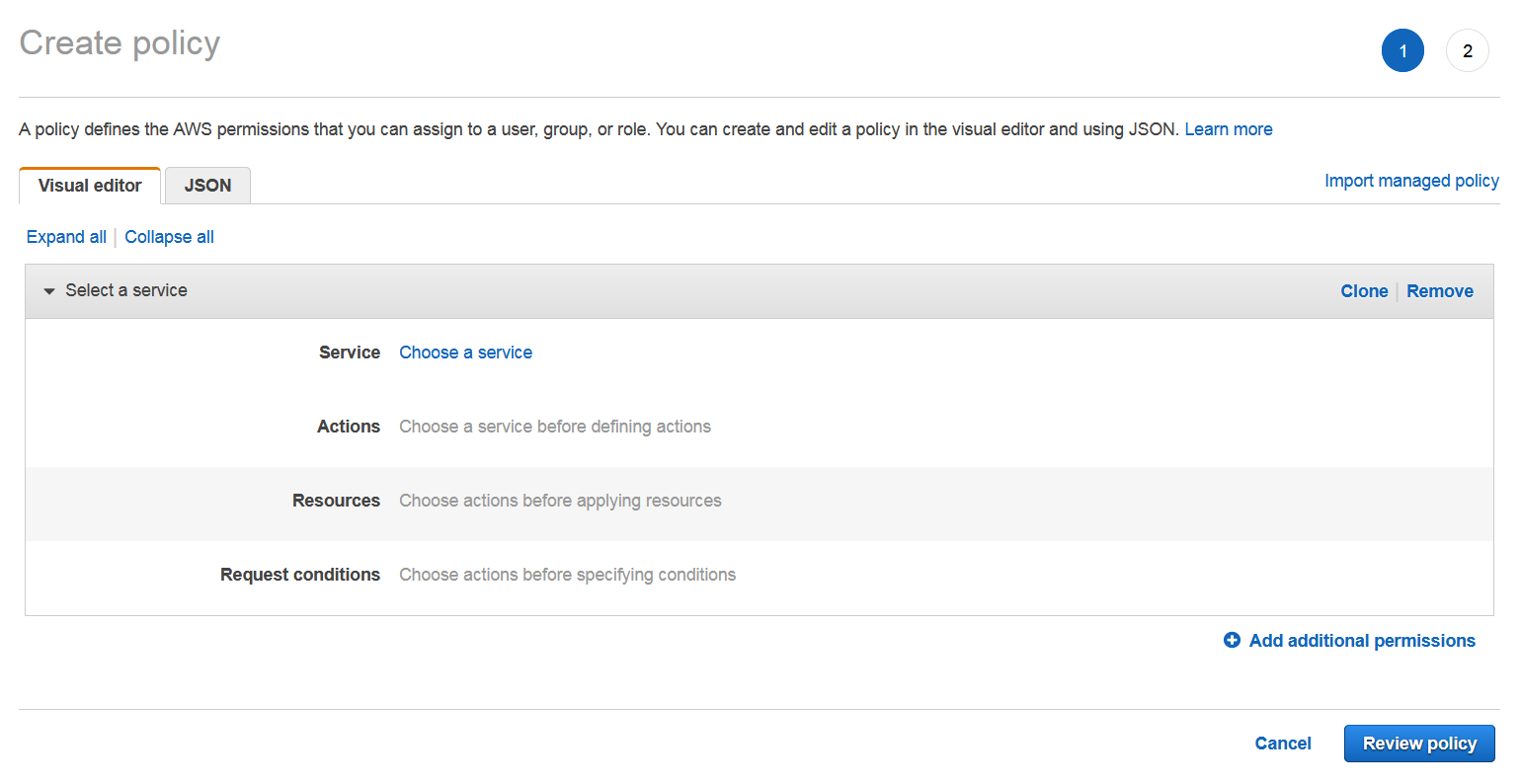
Click on Policies to the left of the AWS console, and click on the Create Policy. This opens the Create Policy page where you can create a new IAM policy.
-
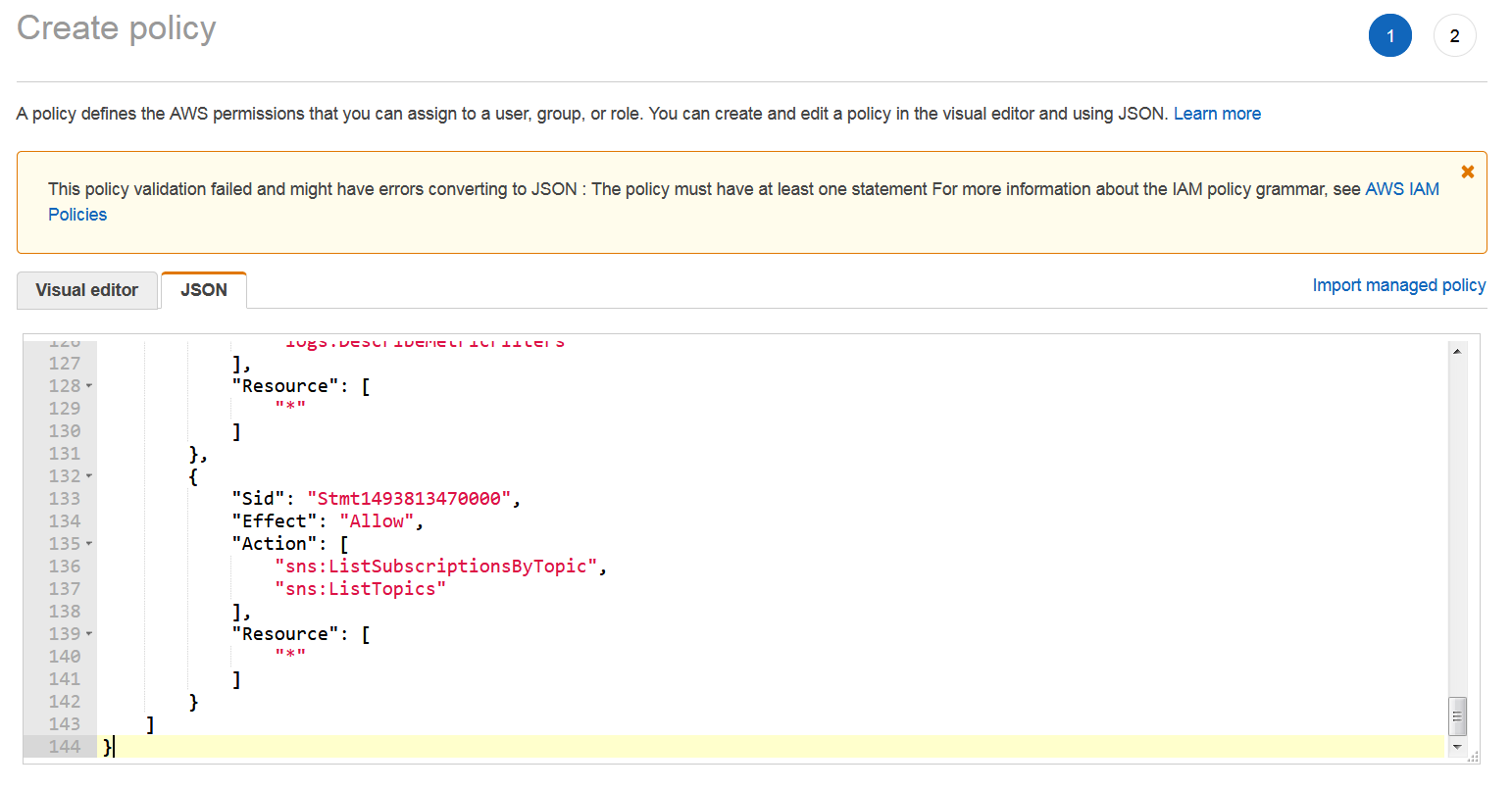
Click on JSON. This opens an IAM policy editor where you can insert your policy.
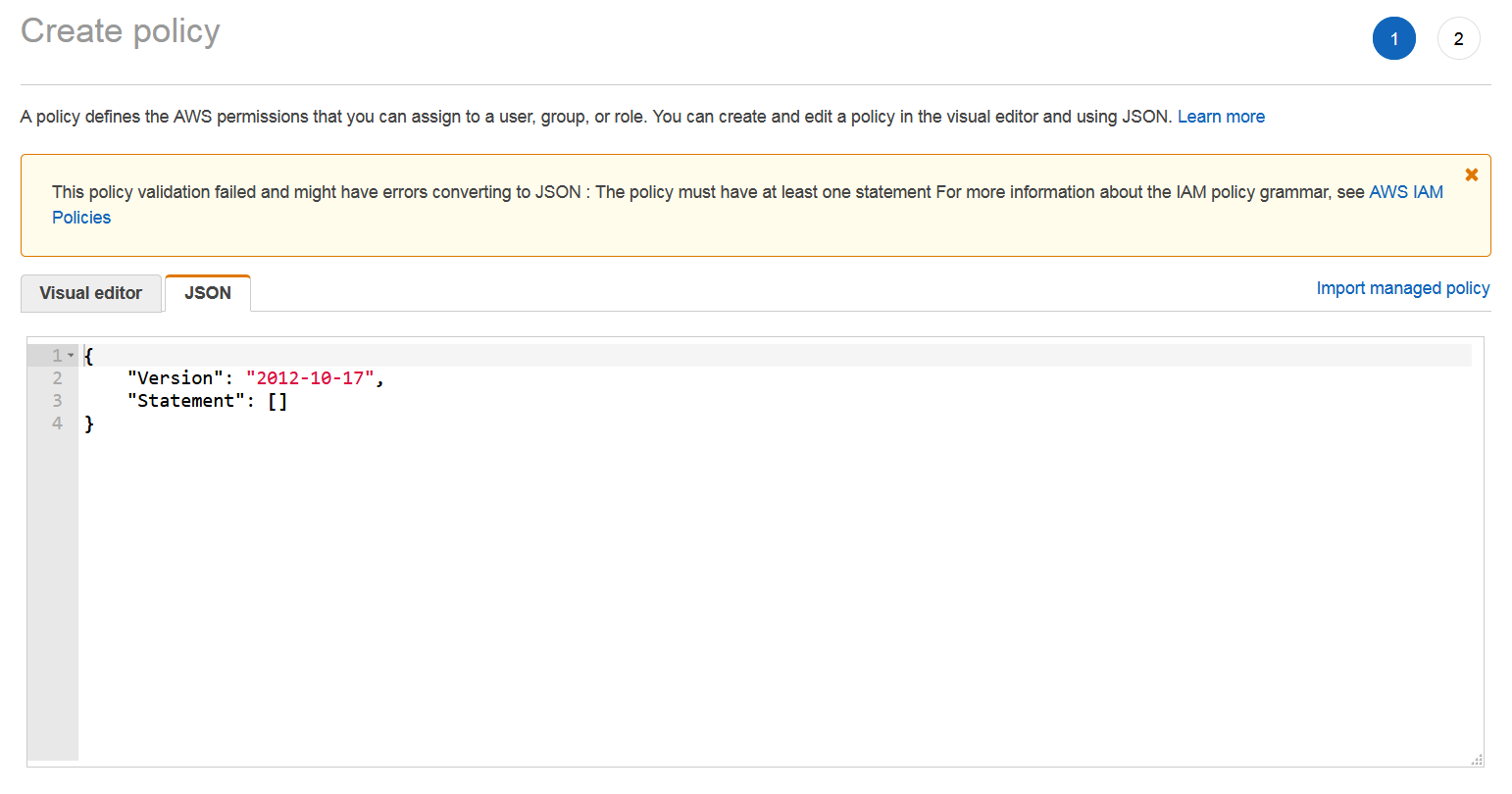
The policy is explained later in this document and can be found in Appendix 1 in JSON Format.
-
-
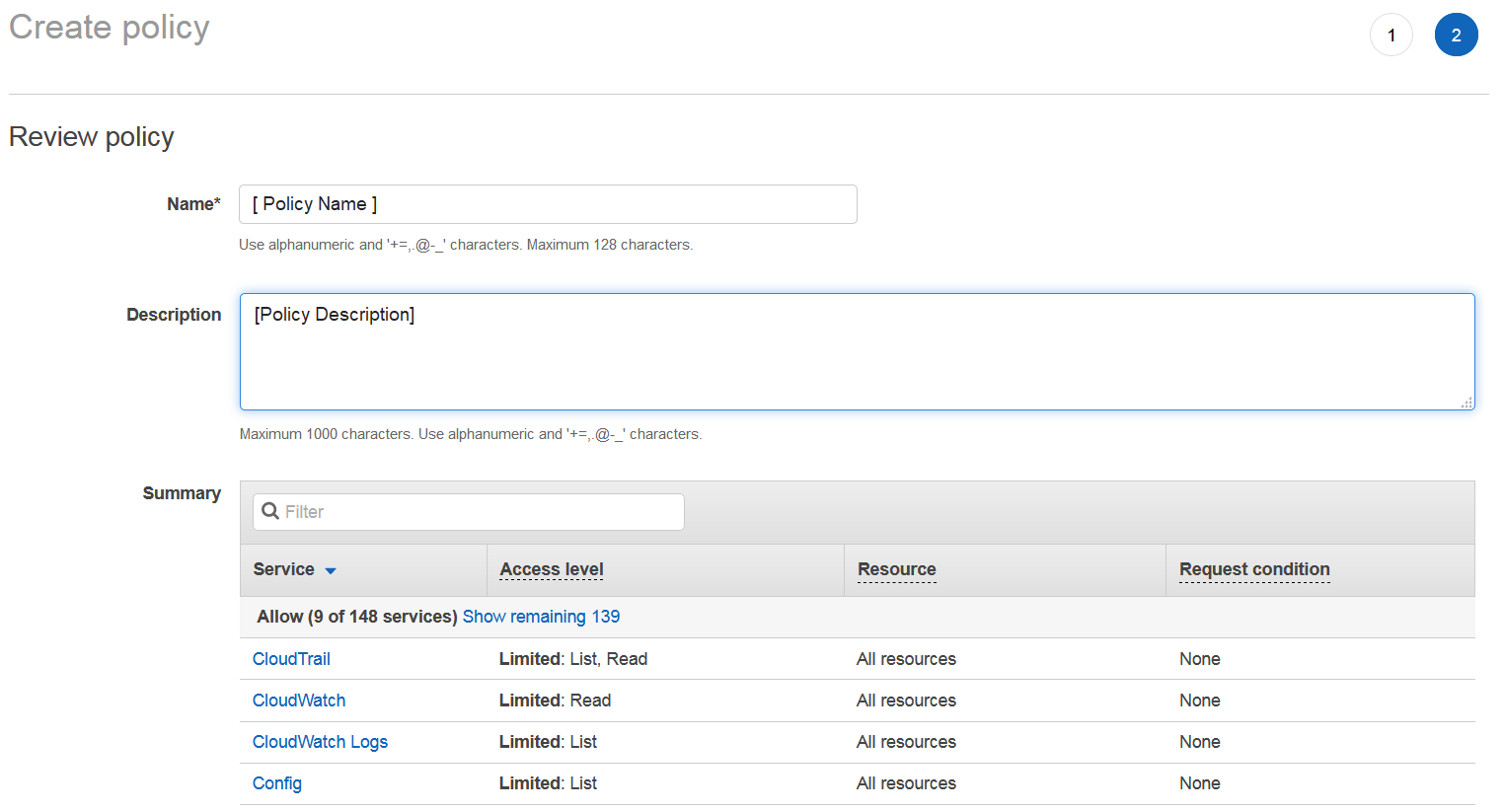
Click on the Review policy button on bottom right and fix Policy Name and Description if your policy is not valid.
-
To validate the policy, click on the Create Policy button.
Create an IAM Role
-
Log in to AWS console and enter IAM Service.
-
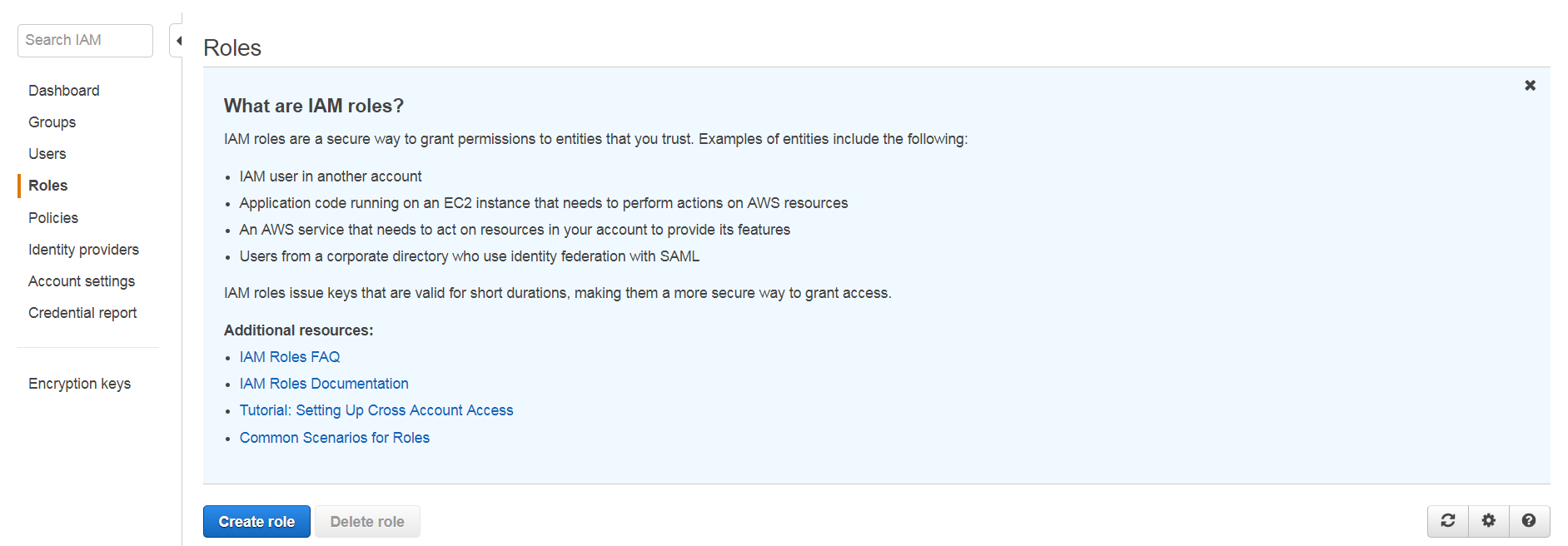
Click on Roles on the left menu and then click on Create role button to open Create role window.
-
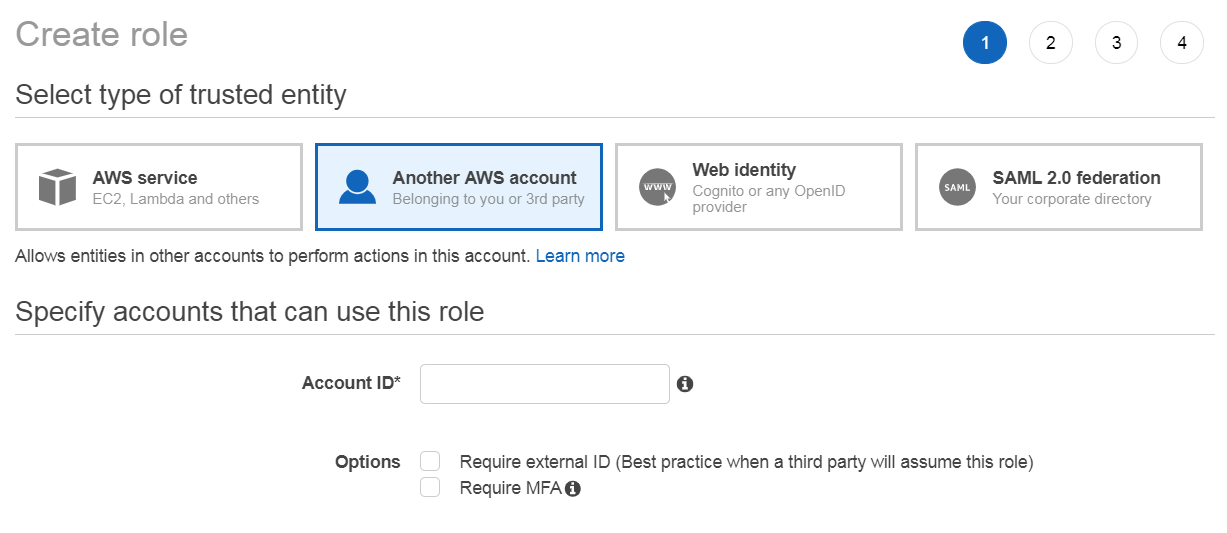
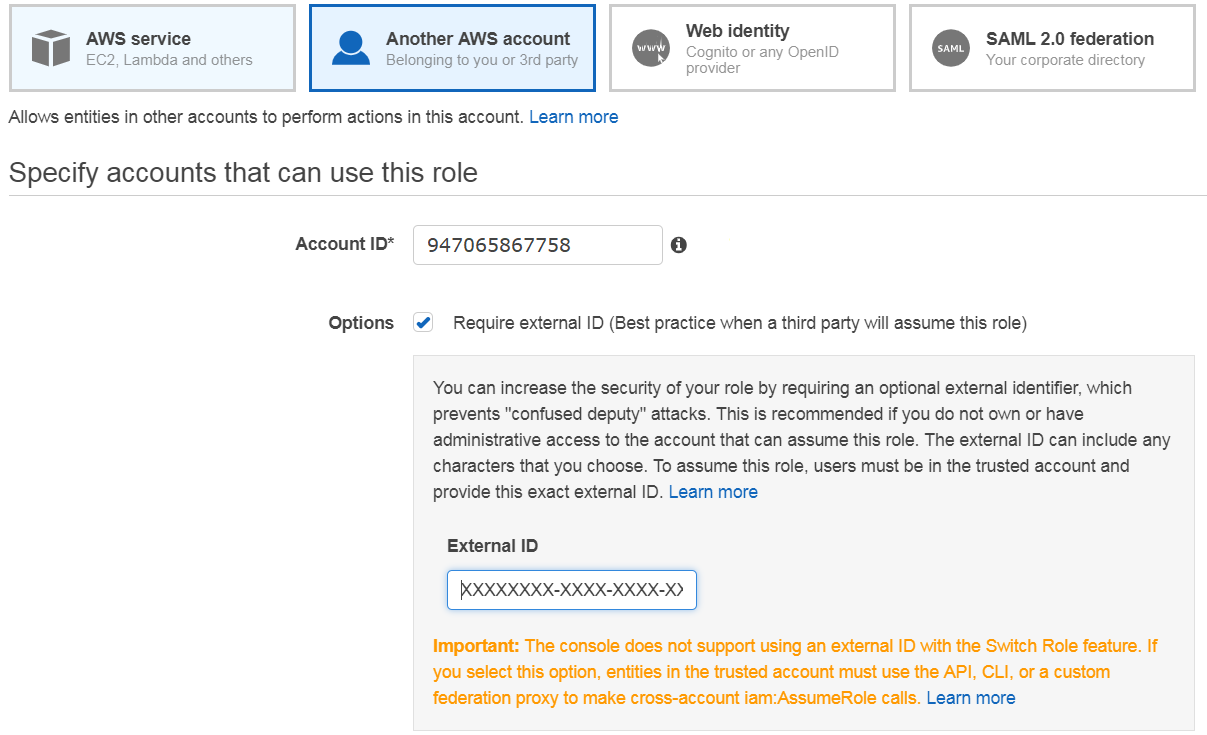
Select Another AWS Account as type of trusted entity.
-
Fill the form using “947065867758” as Account ID.
-
Select Require external ID as Options and use the External ID provided in the Amazon section of Integrations Settings panel in OUTSCAN.
-
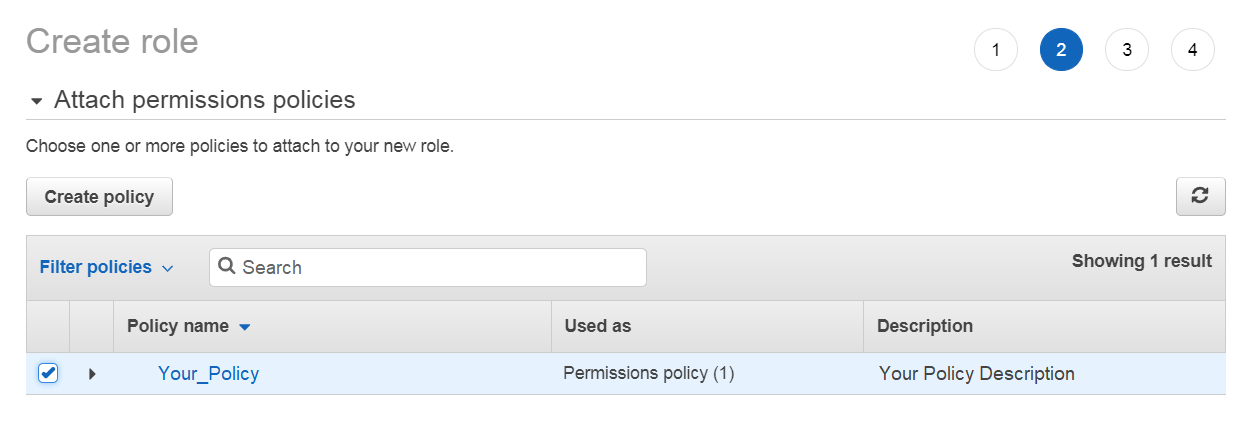
Select the AWS policy you created.
-
Add a name to the AWS role and set a description.
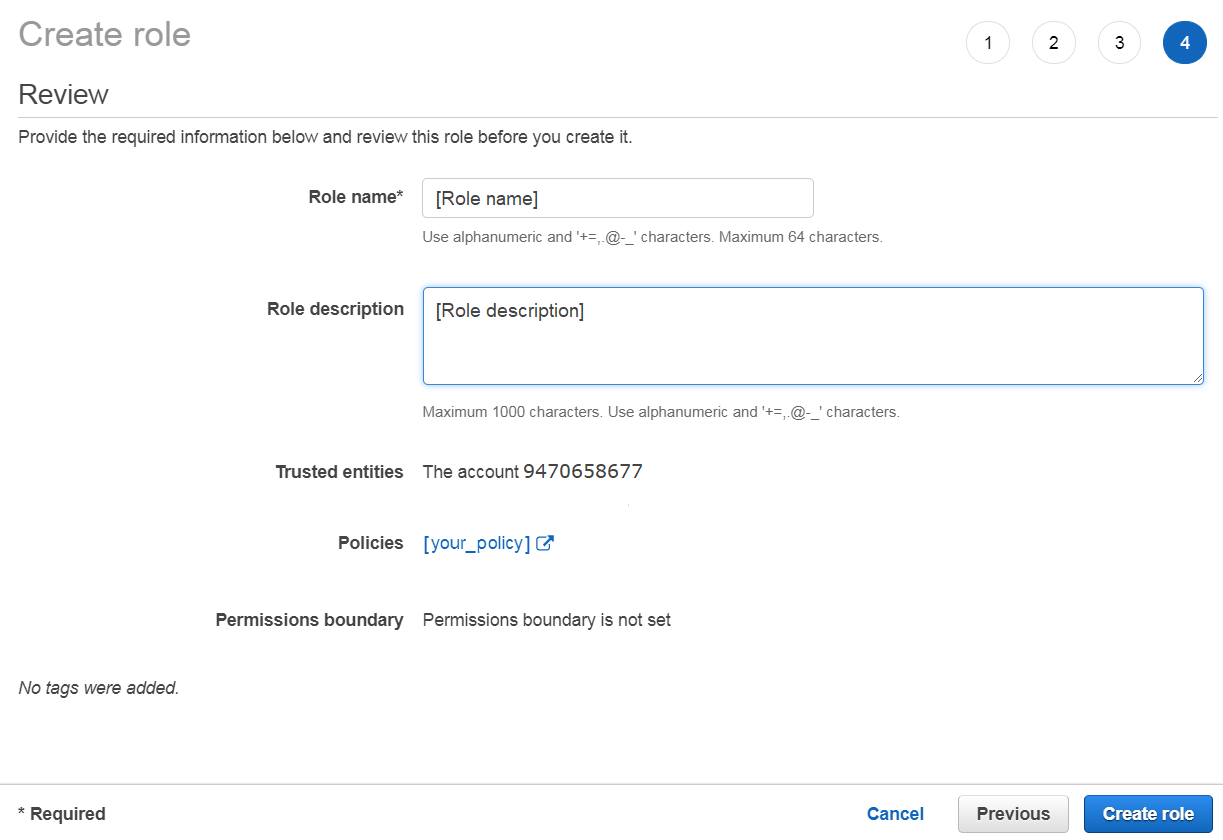
Create AWS role
-
Click on the Create role button on the bottom right.
Adding Credentials
-
Log in to OUTSCAN. See the Logging in to the portal article on how to access the Portal.
-
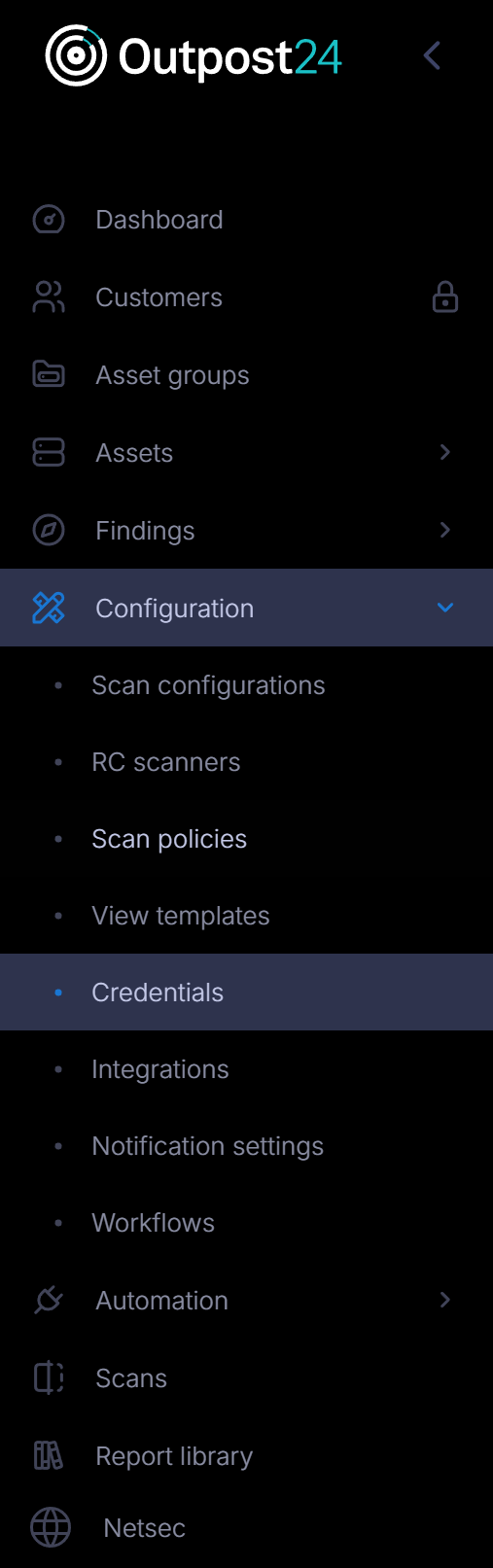
In the Portal menu view, click the Configuration → Credential.
-
Click the Create credentials button to open the create credentials form.
Configure AWS Credentials
Add AWS credentials in Outpost24 using Access Key or IAM Role to allow authenticated scanning of your Amazon Web Services resources.
To manage your account, refer to Scan Credentials.
References
AWS IAM Best Practice:
http://docs.aws.amazon.com/IAM/latest/UserGuide/best-practices.html
AWS IAM Policy Simulator:
https://policysim.aws.amazon.com/home/index.jsp
Appendix-1
The below appendix consists of the AWS Policy for Outpost24 product in JSON format.
|
|
Viewing AWS Policy for Outpost24 software Summary in the AWS Console.
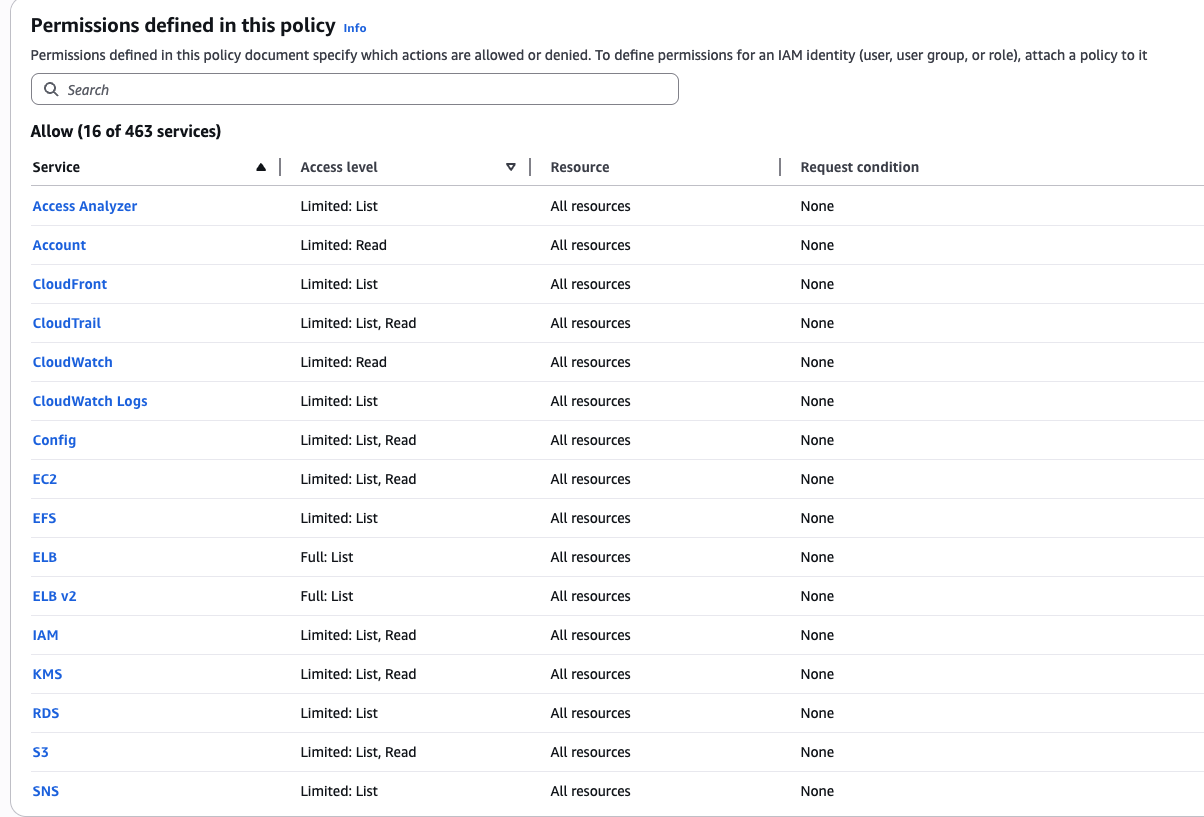
Summary
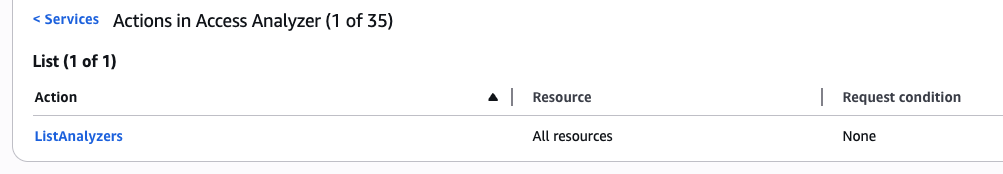
Access Analyzer
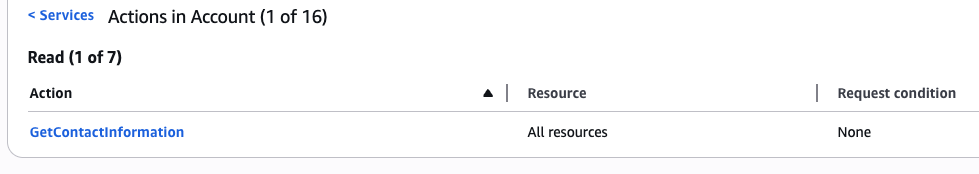
Account
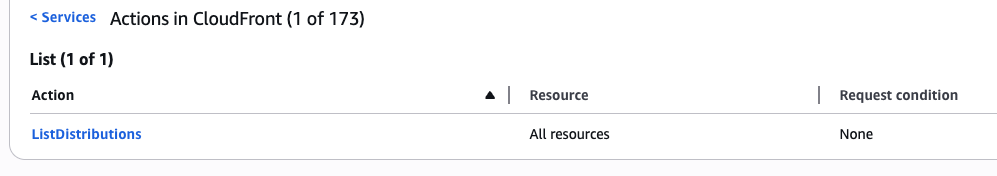
CloudFront
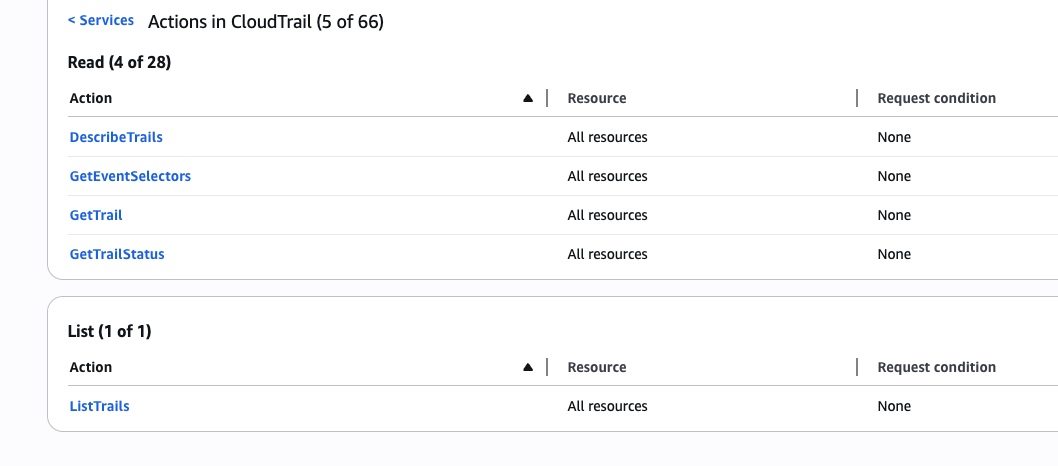
CloudTrail
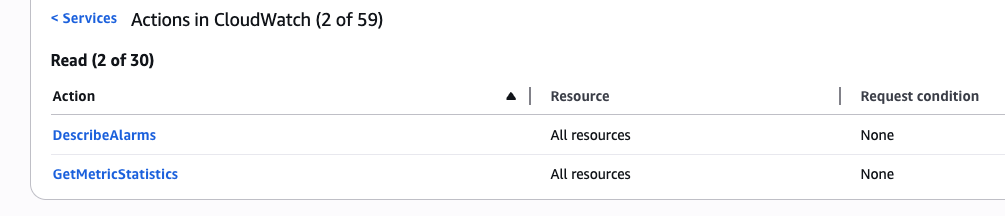
CloudWatch
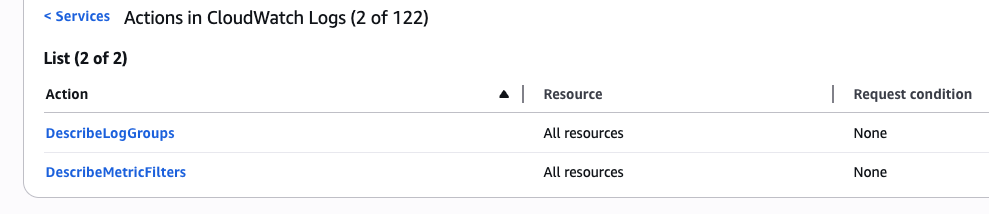
CloudWatch Logs
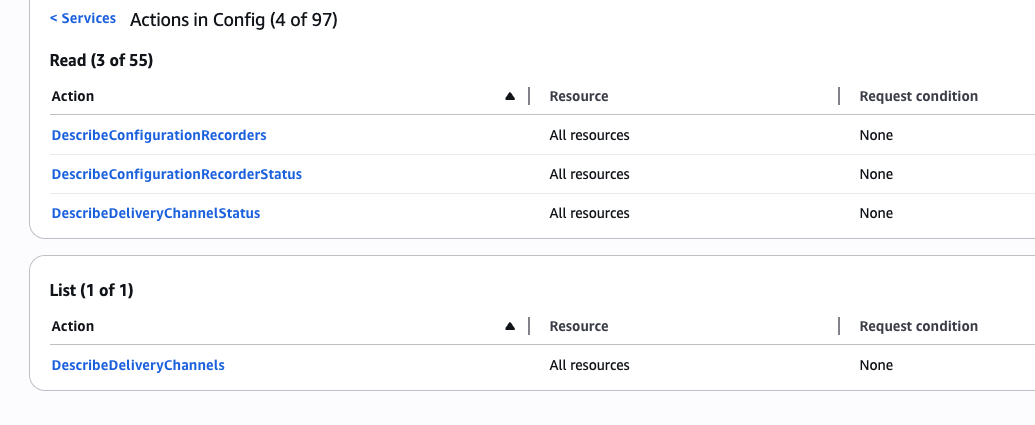
Config
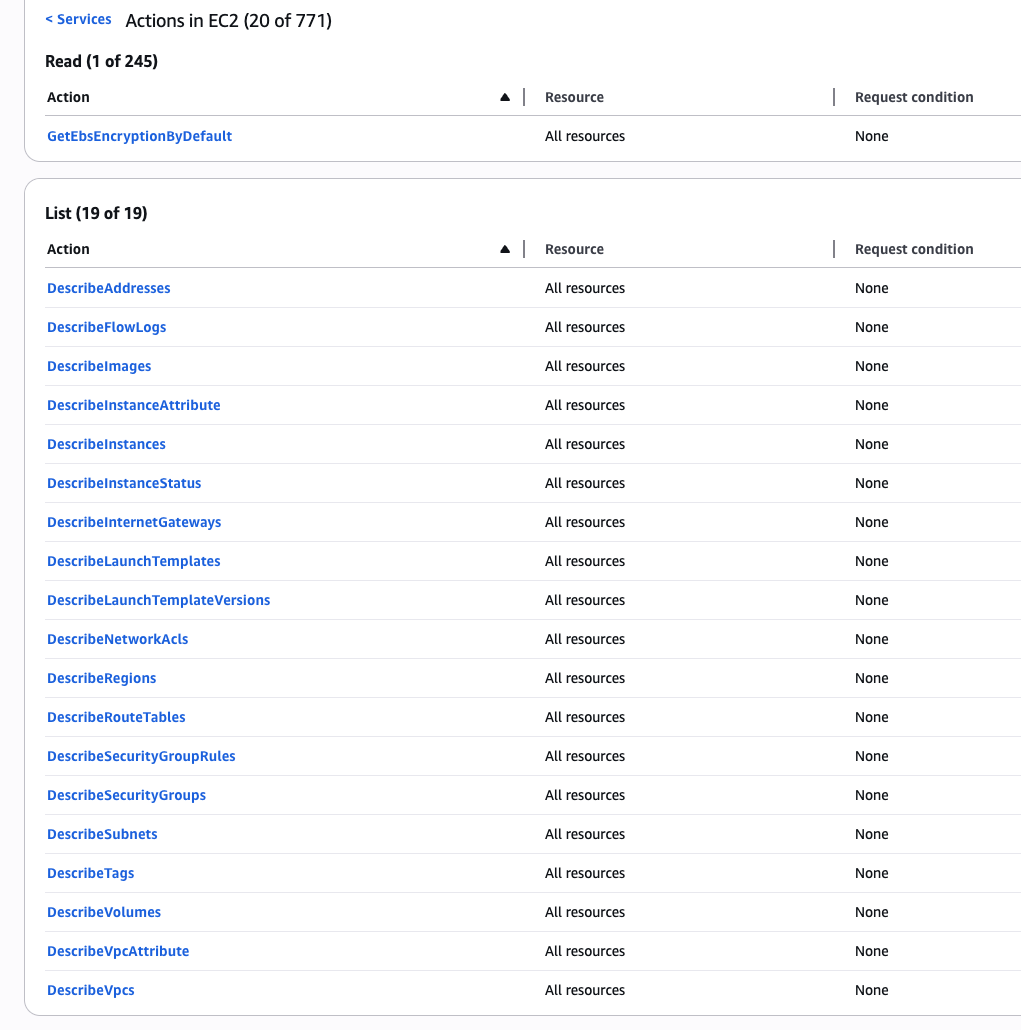
EC2
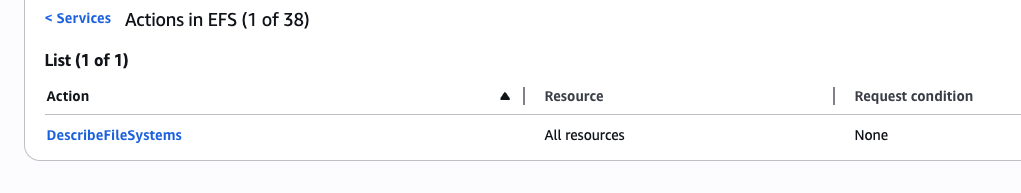
EFS
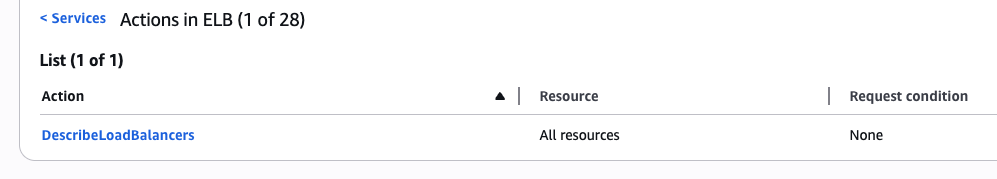
ELB
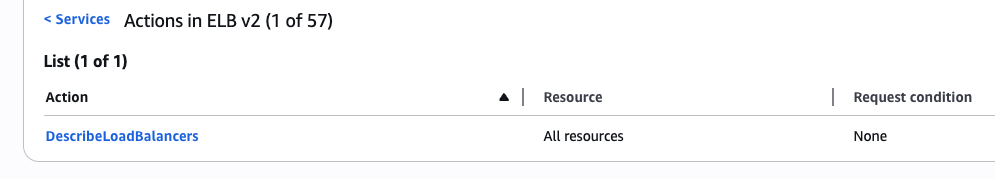
ELB v2
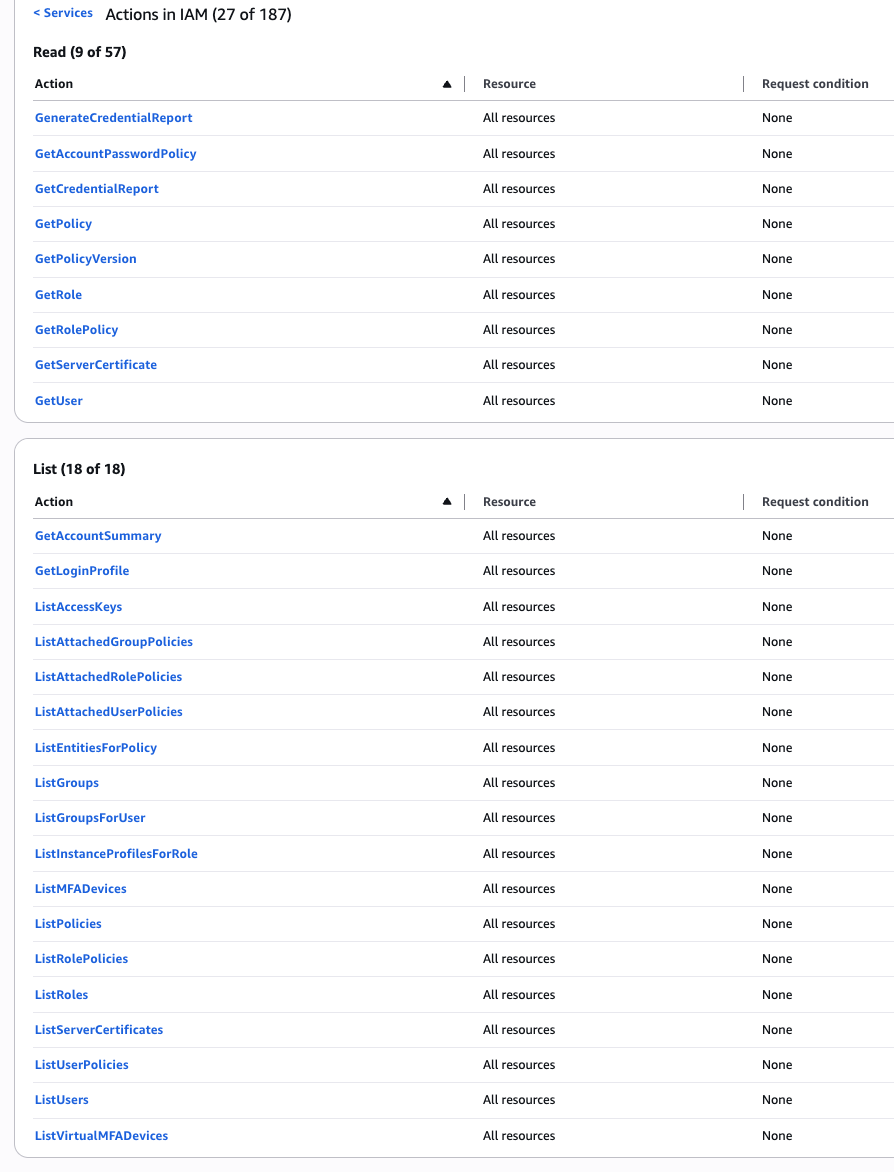
IAM
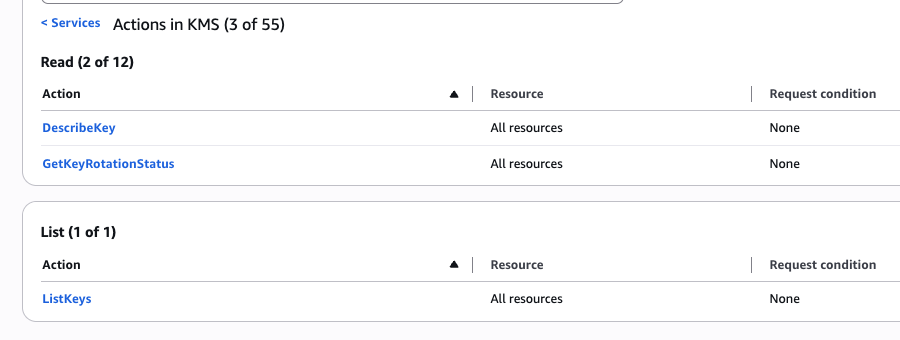
KMS
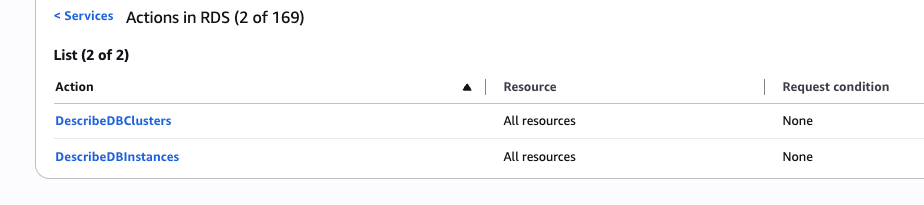
RDS
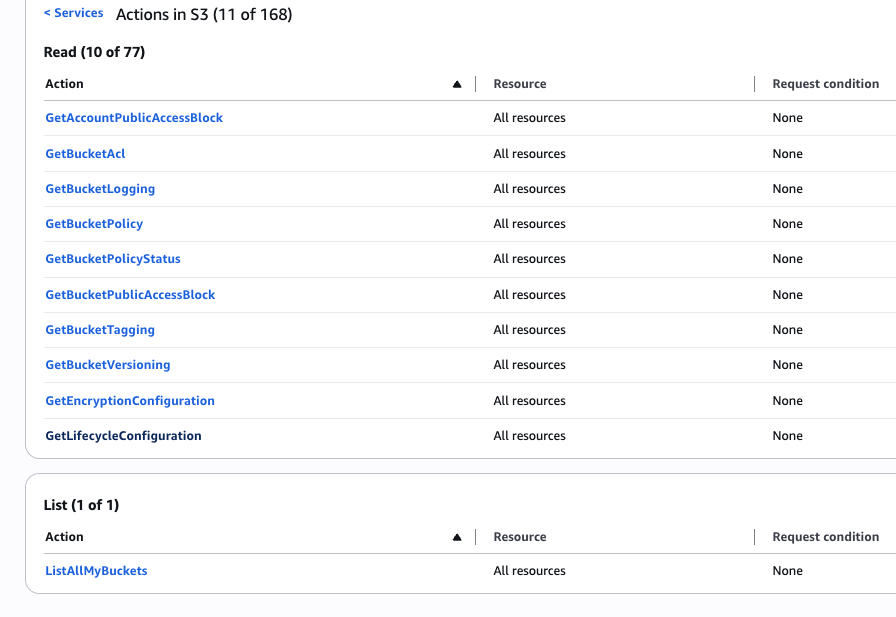
S3
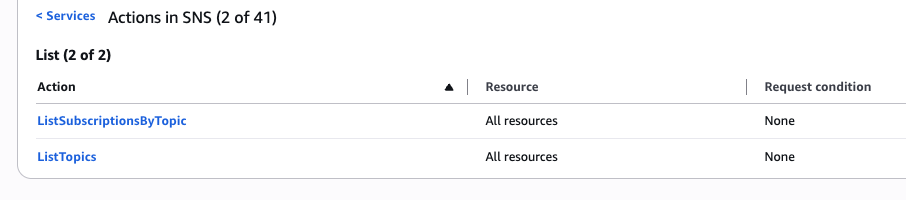
SNS
Related Articles
- Account Settings
- Generate Azure Credentials
- Google Cloud Platform Credentials
- Microsoft Azure Credentials
- ADFS Identity Provider Configuration
- SSH Credentials
- Docker Credentials
- Auditing Guide
- Amazon Web Services Credentials
- VMware vSphere Credentials
- Two Factor Authentication
- Account
- Generate AWS Credentials
- Basic Credentials
- SMB Credentials
