Scout
Purpose
This document provides users with an overview of Scout. This document has been elaborated under the assumption that the reader has access to the OUTSCAN account with Scout subscription.
Introduction
Scout is an asset discovery tool that uses the provided input to find and report on resources and their associations that might have been previously unknown. It enumerates services and deducts information about linked hosts, IPs and other resources that need additional security checks on application or infrastructure layer.
It uses the following methods to gather the data:
Network discovery
Port scanning
Web service enumeration
Software component detection
Subdomain bruteforcing
TLS scanning
Getting Started
To launch OUTSCAN application, navigate to https://outscan.outpost24.com.
Note
Use HTTPS protocol.
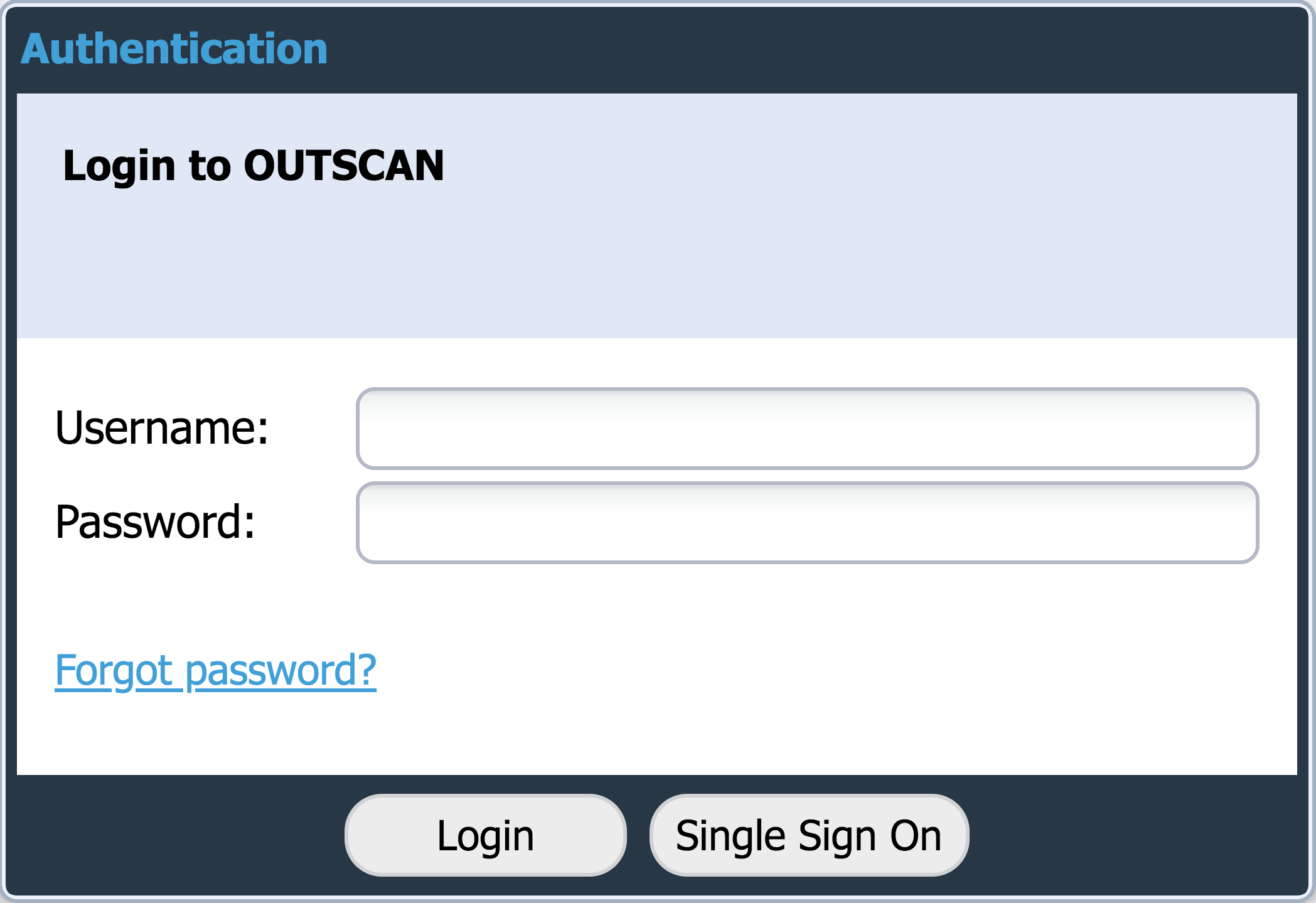
Log in using your credentials.
To access Discovery scanning module, go to Main Menu > Portal to access Scout through the new UI.
Asset Overview
Contact your Sales Engineer for information on obtaining the attack surface score and map.
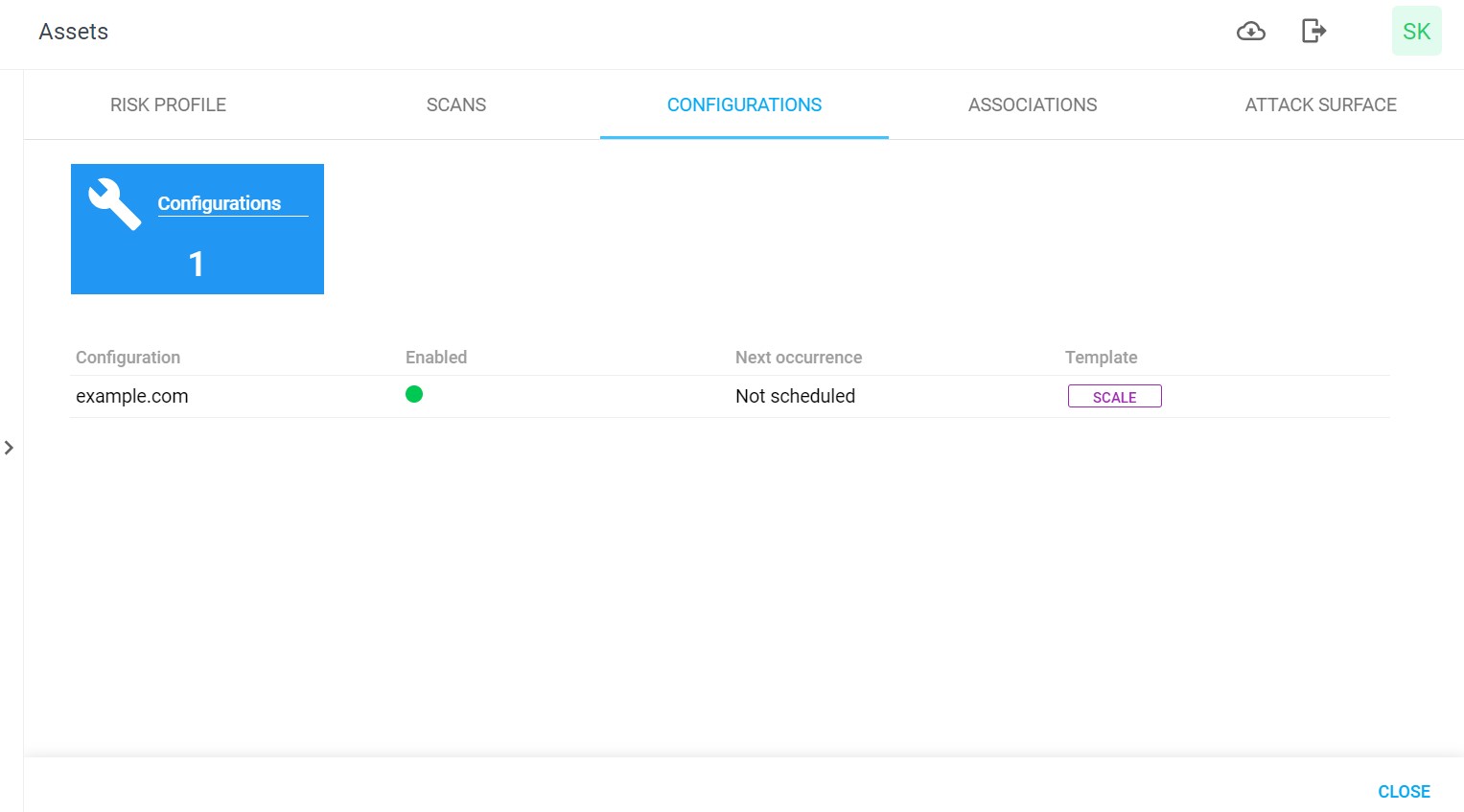
Click on the Name to view the Asset details.
Attack Surface
The user must upload both scores and components (application elements) using the rest API to view the attack surface details in the UI. Under this tab, a spider chart is displayed which depicts the distribution of risk across these 7 elements, and the top most discovered components with their overall Farsight risk.
.png?inst-v=9c616d47-b297-4873-accb-2986cbeb6961)
Manage a Scout Asset
The possible user actions are:
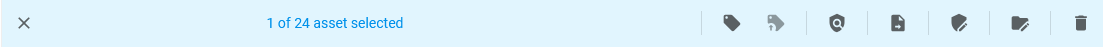
Click on the edit tags
 icon to add, edit, and remove a tag to the selected finding. See Tags for more information.
icon to add, edit, and remove a tag to the selected finding. See Tags for more information.
Recommendation on how to use Tags
Primary Owner
Secondary Owner
Location - Geographical location, Ex: London, Europe.
Function - Such as e-commerce, finance, crm etc.
Impact - Values Critical/High/Medium/Low should describe how the system affects business.
Other examples of useful tags:
Cloud - Is the system hosted in the cloud
Cloud Provider
Contact Info - Can be email of the person to contact about this system.
Click on the update external tags
 icon to add all custom attributes of Agent asset identifiers as tags on the asset, except MAC attribute.. See Tags for more information.
icon to add all custom attributes of Agent asset identifiers as tags on the asset, except MAC attribute.. See Tags for more information.Click on the view related findings
 icon to open a view over findings linked to the selected asset.
icon to open a view over findings linked to the selected asset.Click on the generate report
 icon to download a report. See Reports, for more information.
icon to download a report. See Reports, for more information. Click on the edit environmental CVSS vector
 icon to edit Environment CVSS Vectors.
icon to edit Environment CVSS Vectors. Click on the manage asset groups
icon to add the selected asset to a an Asset group. See Asset Groups for more information.
Delete Assets
Select the assets to be deleted, and click on the delete
 icon at the bottom of the view.
icon at the bottom of the view.Confirm the action by clicking DELETE.
Related Articles
Copyright
© 2025 Outpost24® All rights reserved. This document may only be redistributed unedited and unaltered. This document may be cited and referenced only if clearly crediting Outpost24® and this document as the source. Any other reproduction and redistribution in print or electronically is strictly prohibited without explicit permission.
Trademark
Outpost24® and OUTSCAN™ are trademarks of Outpost24® and its affiliated companies. All other brand names, product names or trademarks belong to their respective owners.
