Purpose
This document describe how to test SMB authentication to a Windows system.
Introduction
When configuring HIAB to use SMB authentication to login to a remote system(s), if the process should fail the error message displayed within HIAB is not sufficiently explanatory to learn if the cause is attributed to a lack of connectivity to TCP port 445 or invalid credentials.
These step-by-step instructions may help to confirm if there is connectivity to the target as well as validate the credentials being used.
Test SMB Authentication
Follow the steps below to test SMB authentication to a Windows system.
Step One
-
From a system running Windows, open a Command Prompt.
-
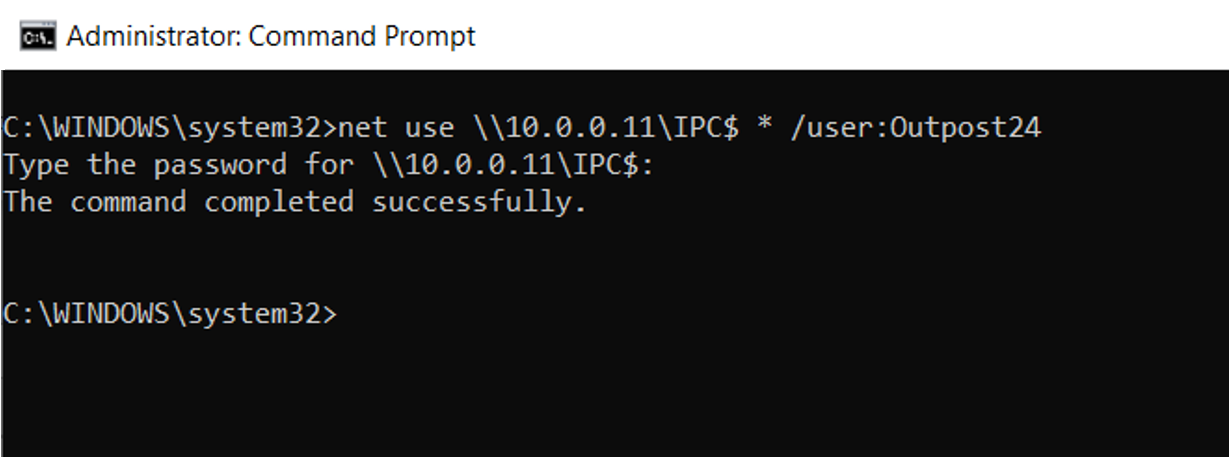
Type
net use \\x.x.x.x\IPC$ * /user:Outpost24replacing "x.x.x.x" with the IP address of the target system and replacing "Outpost24" with the username you need to test authentication with and press Enter. -
When prompted for, type the password for the specified username and press Enter.
-
If the username and password is valid, the text “The command completed successfully.” is displayed before returning to the prompt.
This is an example testing SMB authentication to a remote Windows system with IP 10.0.0.11 using Outpost24 as the username.
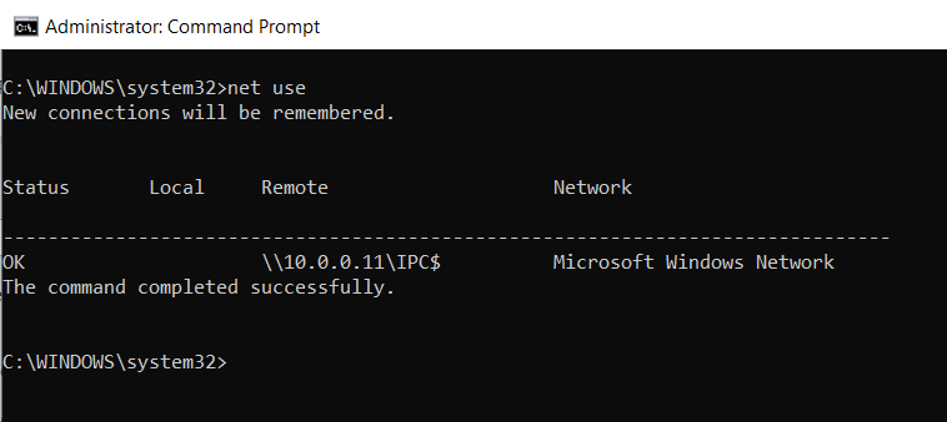
Step Two
Assuming the username and password are correct and after being returned to the prompt, type net use and press Enter to display the Interprocess Communication (IPC$) to the remote Windows system.
If the command completed successfully and the IPC$ share is displayed, then the username and password have been validated to the remote Windows system.
This is an example displaying the IPC$ share to the same remote Windows system from the example above.
Step Three
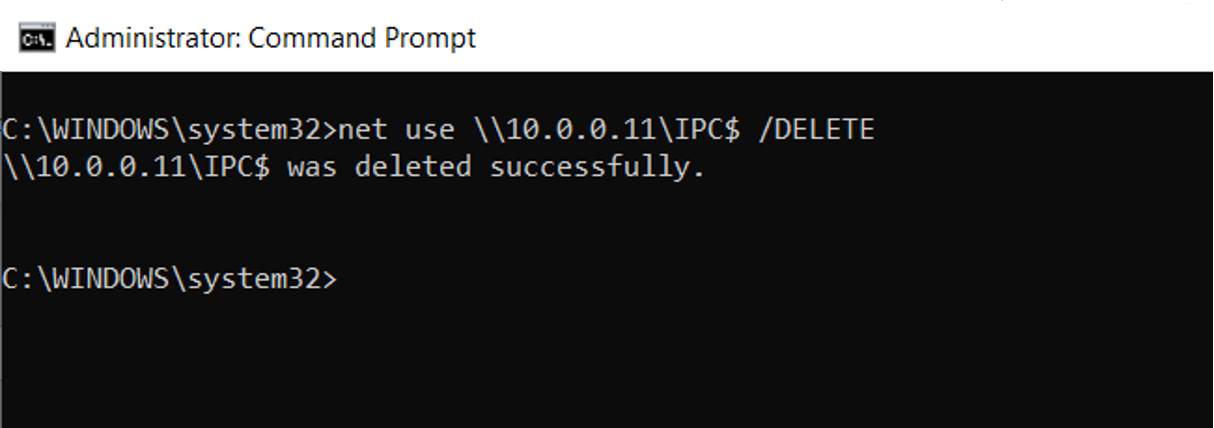
Next type, net use \\x.x.x.x\IPC$ /DELETE replacing the “x.x.x.x” with the IP address of the target and press Enter to remove/delete the IPC$ share to the remote Windows system.
This is an example removing the IPC$ share from the remote Windows system.
Step Four
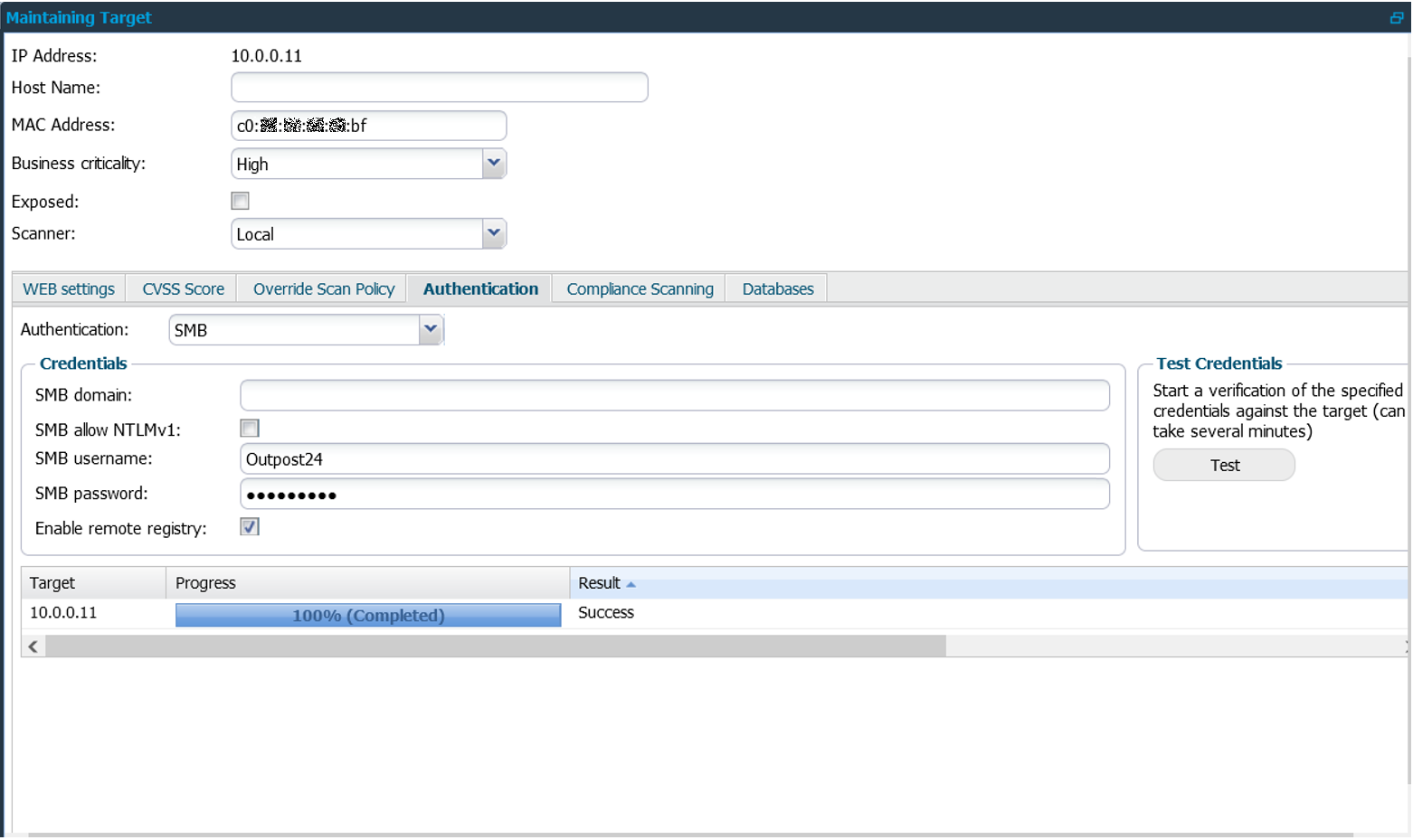
After having successfully authenticated with the username and password to the remote Windows system, the same should be specified for use within HIAB.
Here is an example displaying the success of SMB authentication to the remote Windows system.
Troubleshooting
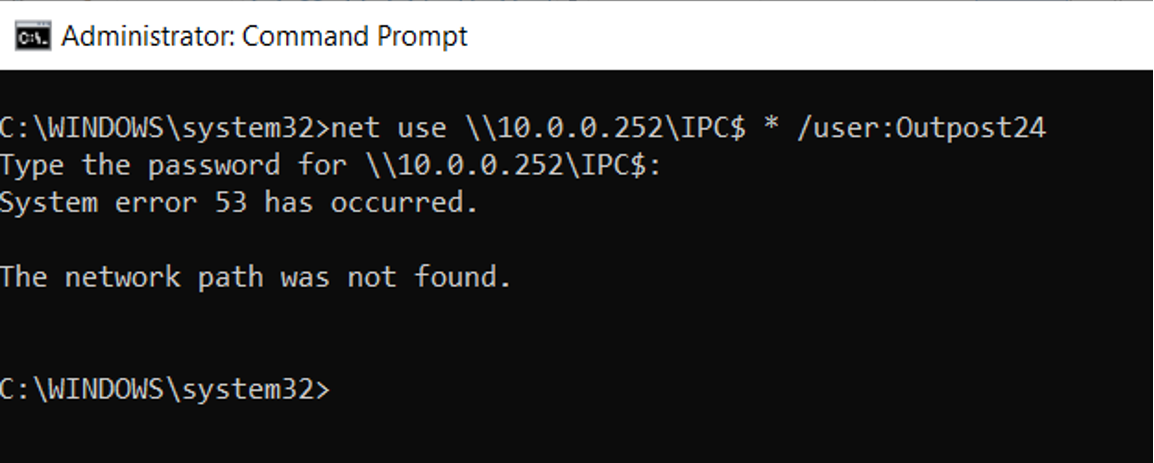
If the target system is not accessible via SMB, despite providing what is thought to be a valid username and password, the response received will be “System error 53 has occurred. The network path was not found”.
If this should occur, check to ensure TCP port 445 is open and accessible on the remote Windows system. One way to test connectivity to TCP port 445 is to use the opensource application Nmap (from nmap.org) as follows: nmap x.x.x.x -p445 --open.
Here is an example of failure because the target system is either not live or port 445 is not accessible.
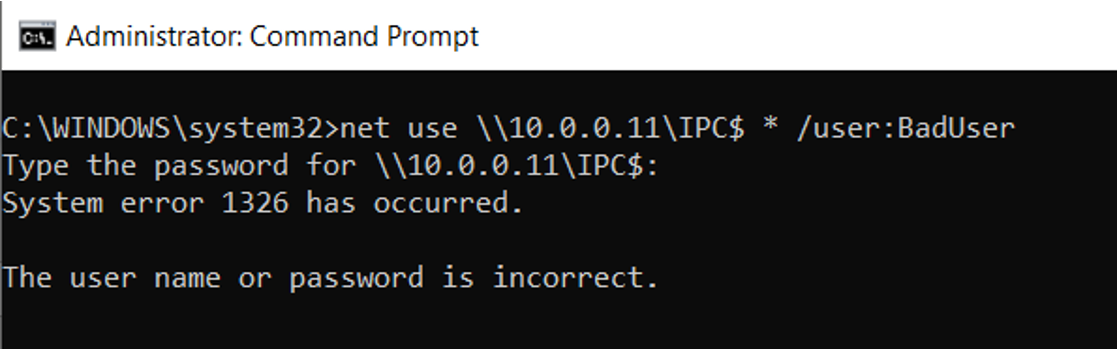
If the target system is accessible via SMB, but the username and/or password is invalid, then there will be a delay until the attempt to authenticate times out, eventually displaying the message “System error 1326 has occurred. The user name or password is incorrect”.
If this should occur, check to ensure the username and password does in fact exist and is a member of the local Administrator group on the Windows system.
Here is an example of failure because the username and/or password is invalid.