Chapter 11: Reports
Reports
To view reports, open the Reports tab in the Pulse web application.
Device Risk Scorecard
The Device Risk Scorecard provides a real-time evaluation of occurrences of threats in your distributed global enterprise, as measured across four security domains:
- Wireless Infrastructure Configuration
- Client Connection Behaviors
- Network Host Configuration
- Shadow IT & Rogue Devices
This report gives you a snapshot of risk areas within your organization, and provides recommendations to mitigate those risks. The scorecard can be viewed through Pulse, or printed using the print icon.
The report offers multiple scoring scales, both letters (like a traditional report card) as well as a 1 to 10 scale.
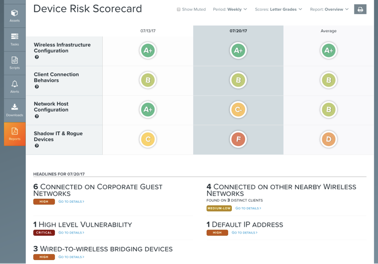
Use the Grade Style drop-down list to change the scoring scale.
Headlines display the most impactful reasons for your scores in any given week. From the headlines, you can navigate directly to the list of assets that generated a specific threat, and begin conducting remediation steps from there.
The scorecard also provides insight into the business risk associated with each finding—it reflects your organization’s susceptibility to data breach, critical network outage and compliance violation. Select Detailed from the Report Style drop-down list.
The Scorecard detailed view supplies additional information that describes not only what led to a particular grade, but also the implications and risks associated with each threat.
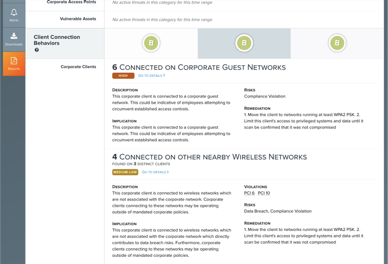
Using the menu at the top, you can jump into any section to get more information about the score. If any finding puts the organization at risk of a compliance infraction, Pulse also identifies the security framework and component that is violated.
For each risk, the criteria is classified according to a defined risk metric, such as an access point running Anomalous Encryption.
For each identified risk, click a grade to display more details about the risk, including:
- Description of the risk and its implications
- The type of risk and the security standards it violates
- Remediation recommendations
Additionally, Pulse automatically generates daily reports that include trending, detail, and summary data for threats and devices detected in by the sensors during the previous day.

To view a daily report, select View to open that report.
You can also export the summary report or full report by clicking Print Summary Report or Print Full Report.
Copyright
© 2025 Outpost24® All rights reserved. This document may only be redistributed unedited and unaltered. This document may be cited and referenced only if clearly crediting Outpost24® and this document as the source. Any other reproduction and redistribution in print or electronically is strictly prohibited without explicit permission.
Trademark
Outpost24® and OUTSCAN™ are trademarks of Outpost24® and its affiliated companies. All other brand names, product names or trademarks belong to their respective owners.
